In this article i have collected few information that we need to look into while we are planning for Exchange Servers across different subnets.
Exchange servers will work perfectly fine on different subnets. As long as there is no firewall interruption between Exchange servers in the subnet you should be fine.Even if you have firewall it will work fine but ensure that you have DC and GC connectivity if you have firewall to these servers since exchange needs them to contact frequently.
But keep in mind the exchange servers need to talk to each other almost constantly and that would just make things extremely difficult and make troubleshooting harder if you run into any issues with Exchange and GC/DC connectivity.
Ensure that there is no Windows Firewall or A/V interfering perhaps between 2 subnets. Let’s have a look at few things that we need to consider during our planning.
For DAG –
If I’ve got servers on multiple subnets do I need to have a DAG IP in the range of each subnet ?
There needs to be a new Subnet added to the DAG before the node in a different subnet can join the DAG.The reason for this is so the DAG name can be switched and hosted in either of subnets.
MAPI network and Replication Network should not be on the same subnets. Having them on a different subnets will not be single point of failure. When a replication network fails, replication should automatically fail-over to the DAG’s MAPI network .Always, DAG member which communicates with other site requires each site with different Replication Network Subnet.
Probably you can perform the below tasks as a part of checking to ensure that the DAG configuration is correct
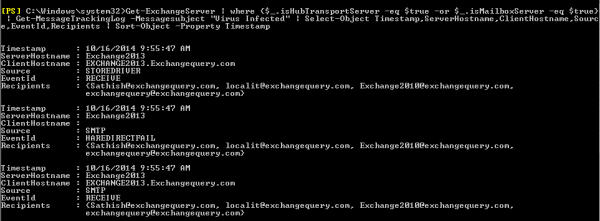
Run the below command to check the network settings of DAG :-
Get-DatabaseAvailabilityGroup -Identity DAGNAME | ft DatabaseAvailabilityGroupIpAddresses
To provide network connectivity between each of the replication subnet, a persistent static route must be entered into the Exchange member’s routing table.
To create a persistent static route run the below command :-
netsh interface ip add route (Example IP)10.3.0.0/ 24 “replication 1” 10.4.0.2
netsh interface ip add route (Example IP)10.4.0.0/ 24 “replication 2” 10.3.0.2
Validate through Failover Cluster Manager and ensure that DAG IP is Online.
For CAS Array –
CAS Array is site Specific
It is possible to add 2 CAS Servers belonging to different subnet in a CAS Array but they should be in same AD sites. Since they should be querying the same DC’s so we can have Exchange servers spanned across 2 datacenters in a single site if you are planning for adding cas servers in a array in 2 different subnets.
If it is going to be 2 different subnets and different sites then we need to create 2 different CAS array one in each site and probably need to do a DNS round robin which will not give a full HA even by setting the TTL values.
For HUB –
We need to have hub servers in each site and they are site specific.Hub servers can support HA for different subnets and help in mail routing only when they are spanned across the same site in different datacenters.
If we are planning for HA for hub servers in different subnet and different site then we need to install hub servers on each site for HA.
The above points will be useful while we plan for Exchange server deployment in 2 sites and subnets.
Reference –
Thanks
Sathish Veerapandian
MVP – Exchange Server