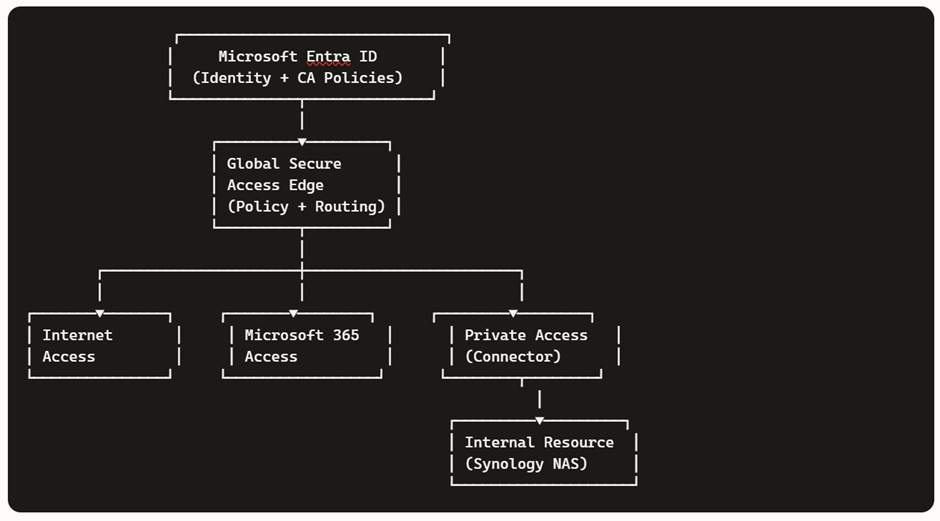
Microsoft Entra’s Secure Web Gateway (SWG) capabilities under Global Secure Access (GSA) are expanding rapidly. One of the newest additions visible in the portal is the “Scan with Purview (Preview)” action inside Content Policies.
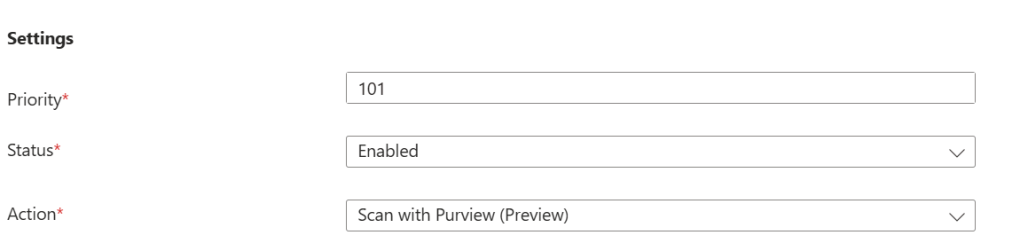
This feature represents a major step forward:
Inline, real time file upload scanning using Microsoft Purview’s classification engine directly inside Entra Secure web gateway (SWG). This helps organizations better protect sensitive files in transit.
By integrating Entra Secure Web Gateway with Purview, organizations gain the ability to inspect file transfers at the network layer and enforce DLP rules in real time. This prevents sensitive data from leaving the organization through untrusted cloud apps, regardless of whether the upload happens via a browser, desktop application, API, or add‑in
This feature as it appears today in preview, based entirely on observable behavior in a Microsoft 365 E5 tenant.
Because this is a preview feature, some components are still evolving, and full functionality is expected to be available by mid June when the feature reaches General Availability (GA) and when the tenant gets this feature completely enabled.