In this article we will go through the steps to enable DKIM in pure office 365 cloud environment.
For understanding DKIM concepts and Enabling DKIM in on premise environment you can follow my previous blog
The main difference between enabling DKIM in on premise environment and office 365 is:
- In on premise we keep the private keys in our outgoing Anti spam gateway or DKIM agent which will be responsible for signing every outbound emails with DKIM stamp. Later we publish the public key in the DNS record.
- But office 365 requests the customers to publish the CNAME and point them to a public key in DNS which will delegate the corresponding name space to office 365.
With this office 365 CNAME option we can rotate the keys whenever required. Because in this case the private key is owned by Microsoft and the public key is maintained in their office365 DNS records. We just need to create CNAME in our DNS console only for the first time. Later we need to create CNAMES only for the new domains we are adding in office 365.
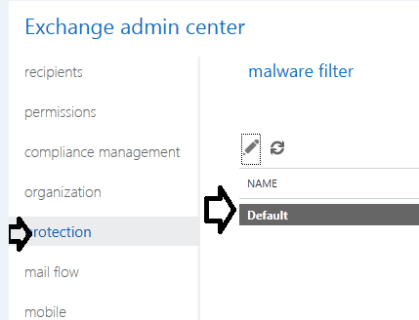
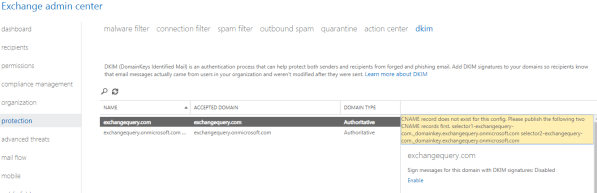
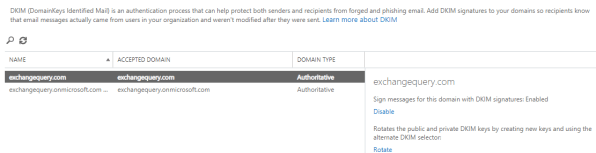
First we need to enable DKIM from the Exchange admin center from the office 365 portal – navigate to protection – click on DKIM tab
We can enable for the routable domains registered with office 365. But when we enable them without publishing the DNS records for DKIM then we will get the below error.
We have to publish DKIM DNS records as below:
Create 2 CNAME records for 2 selector’s to sign the outgoing emails with DKIM.
In our case we need to create below records from the DNS hosting provider console.
Host name: selector1._domainkey.exchangequery.com
Points to address or value: selector1-exchangequery-com._domainkey.exchangequery.onmicrosoft.com
TTL: 3600
Host name: selector2._domainkey.exchangequery.com
Points to address or value: selector2-exchangequery-com._domainkey.exchangequery.onmicrosoft.com
TTL: 3600
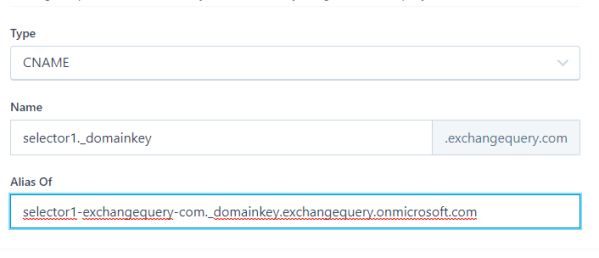
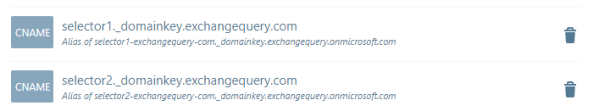
Once we create these 2 CNAME records office 365 will take care of signing all the outgoing emails with DKIM with their signing agents.
Now if we go to office 365 portal and enable the DKIM it will get enabled. If we have a closer look we have an option to rotate DKIM keys just in one radio button which is amazing option. Ideally its not required to do this option from our side since office 365 will do the rotation of their keys once in a while as a part of their security checks.
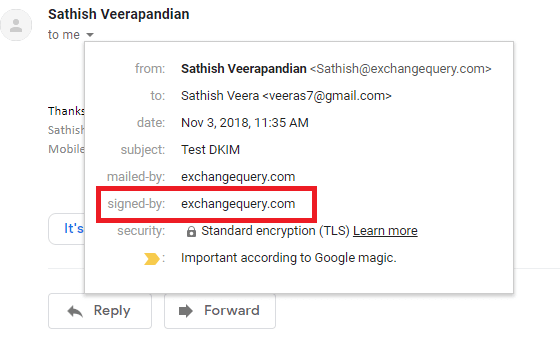
To verify if the mail is signed by DKIM we can send one test email to gmail and if it says signed by your domain name then its DKIM enabled outbound email.
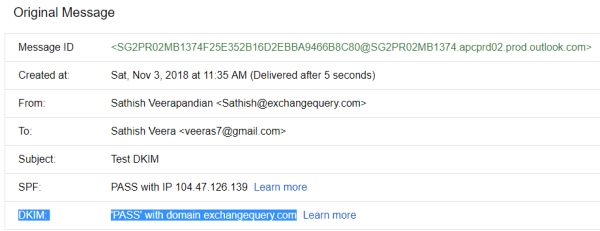
In the message headers we can see the DKIM status as passed.
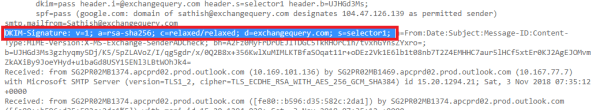
Further if we look into the message headers we can see
Authenticated Received Chain (ARC)- New email security mechanism standard Which is currently used by office 365.
DomainKeys Identified Mail (DKIM)- If the DKIM is enabled we see the DKIM value as pass.
Sender Policy FrameWork(SPF)- SPF verification results.
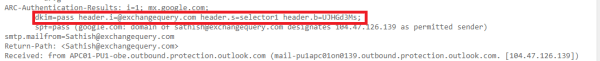
Also in the DKIM signature we can see the selector and the domain name like below
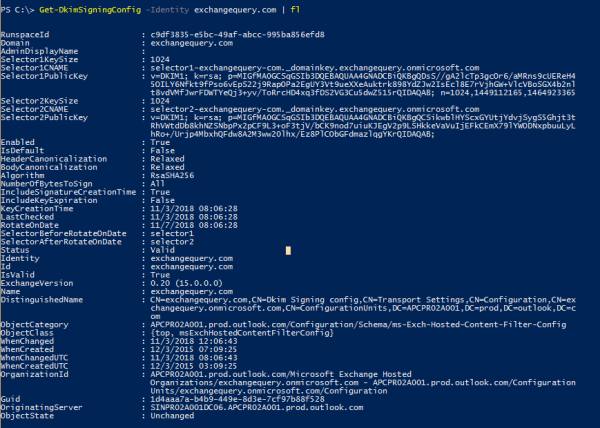
Further we can look into the DKIM public keys by running the below command.
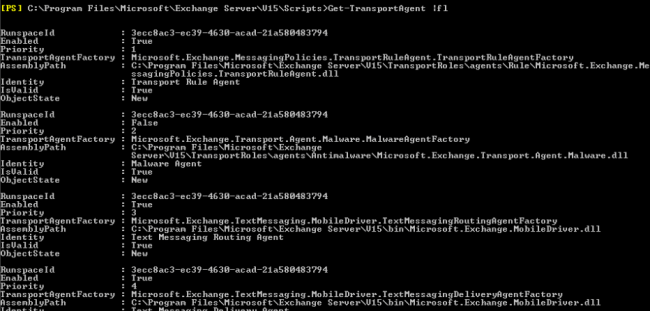
Get-DkimSigningConfig -Identity exchangequery.com | fl
Additional General Info:
Below can be the possible results as a part of DKIM test in the message header.
- DKIM=Pass – Message was Signed.
- DKIM=Fail – The message was signed and the signature or signatures were acceptable, but they failed the verification test(s).
- DKIM=None – The messages were not signed.
- DKIM=Policy – The messages were signed but the signatures were not acceptable.
- DKIM=neutral = The message was signed, but it was not formed correctly. This is possibly a configuration error on the sending domain side.
- DKIM=temperror – This is a temproary error where unable to verify the public key for the DKIM verification.
- DKIM=permerror = The message could not be verified due to some error that is unrecoverable.