Microsoft intune is a cloud service which was introduced in office365. This intune service is charged per user license. It can be configured for cloud only users as well as hybrid users.
Intune can be used for end users end point protection, MDM ,MAM ,application distributed storage, software license inventory reports , hardware inventory reports , mobile device app publishing, security monitoring.
This blog focuses only on configuring the in tune MDM\MAM for cloud only users to secure the office 365 services configured in mobile devices.Using this we would be able to enroll Mobile devices, manage devices and applications, protect the corporate data and retire them when required.
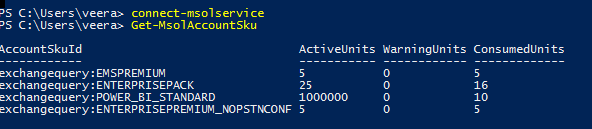
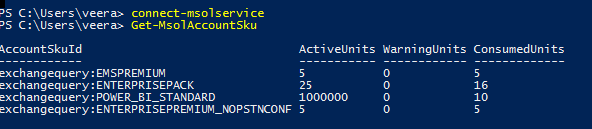
First thing is to see the license required for intune to assign them to end users.
Get-MsolAccountSku
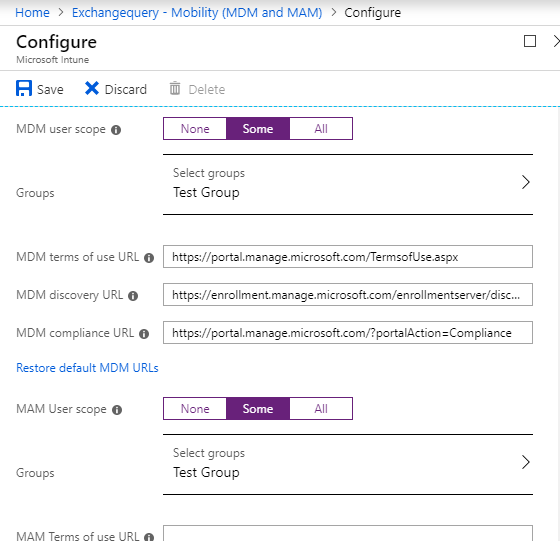
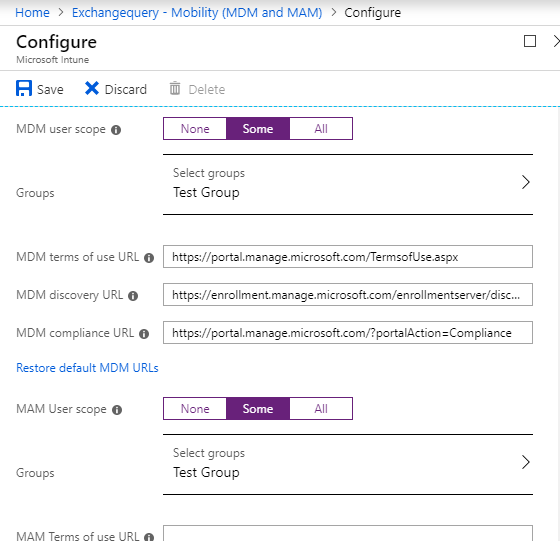
We need to see the MDM user Scope set in the azure portal.
https://portal.azure.com
By default it is not set to any users. We can create a group and assign the scope to the group. This will perform the MDM enrollment for Android, iOS devices.
Here we have three URL’s:
- MDM/MAM Terms of use – Can be used to set company terms of use.
- MDM/MAM discovery URL – This is the device enrollment URL.By default it is set to office 365 enrollment url and can leave them as it is if you are using only intune as MDM/MAM service.
- MDM/MAM Compliance URL– URL to be used to give more information to users on why the device is non-compliant if it doesn’t meet the standards.
All the above options can be customized based or left blank based on the current MDM/MAM setup. If we are rolling out the MDM/MAM first time for all users then we can leave these url’s as default and can update only the terms of use and compliance url as per the company’s security policy.
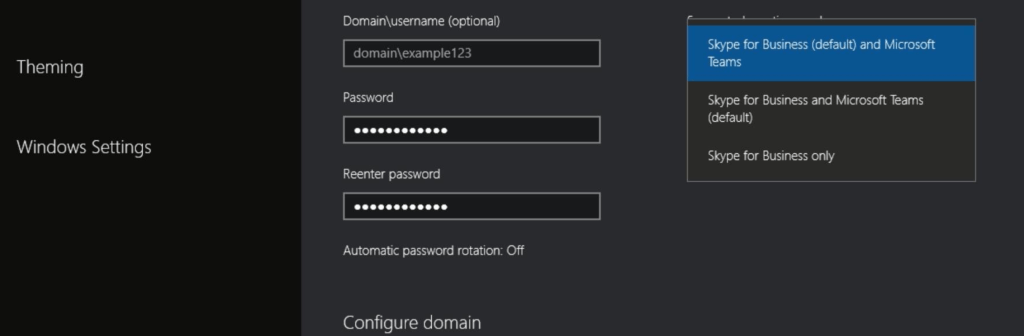
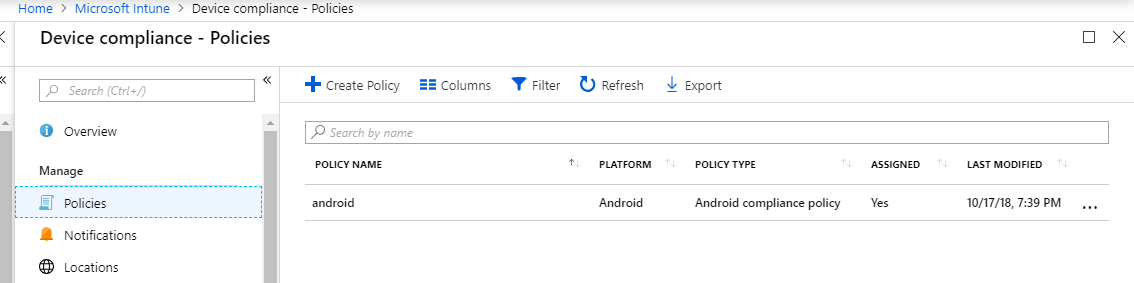
Now we need to create below policies:
- Device Compliance Policy –To manage compliance for IOS & Android devices.
- Device Management policy- for IOS and Android device management.
- App Protection policy-Can be created to protect targeted apps only.
- Client Apps – Can be used to assign curated managed apps, such as Office 365 apps, to iOS and Android devices
- Create one Conditional Access Policy for MDM (Optional)– Can be enforced to use only Outlook for IOS Andriod, restrict logins from geo locations.
Create Device Compliance Policy-
We need to navigate to the https://portal.office.com – Admin – Select Microsoft Intune and navigate to intune blade
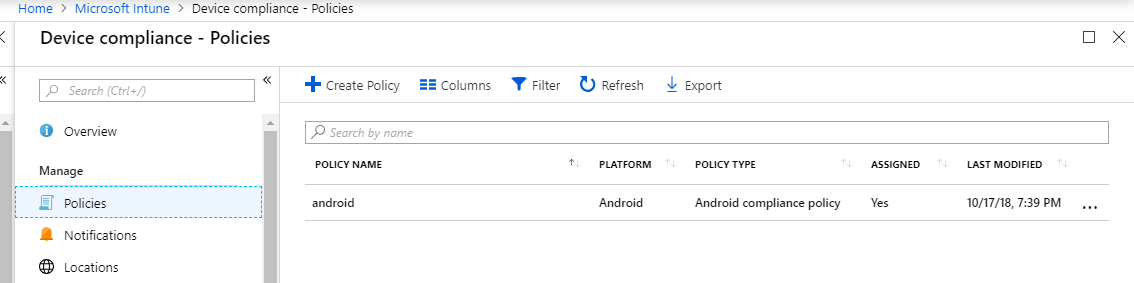
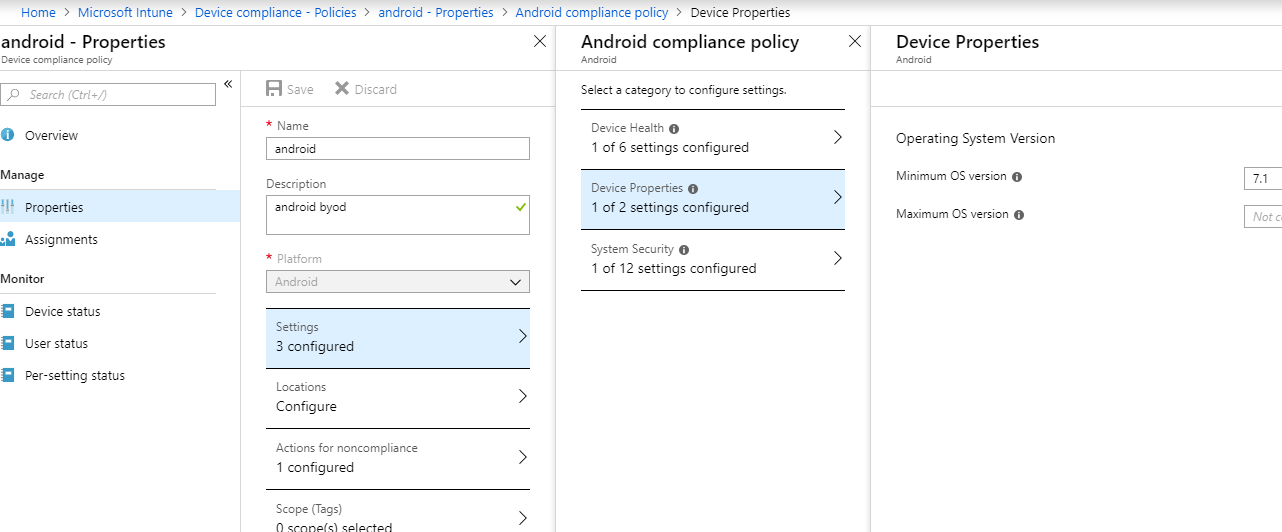
We need to create compliance policy for Android and IOS devices.Example below for Android where the minimum version is 7.1 and blocking rooted devices can be done.
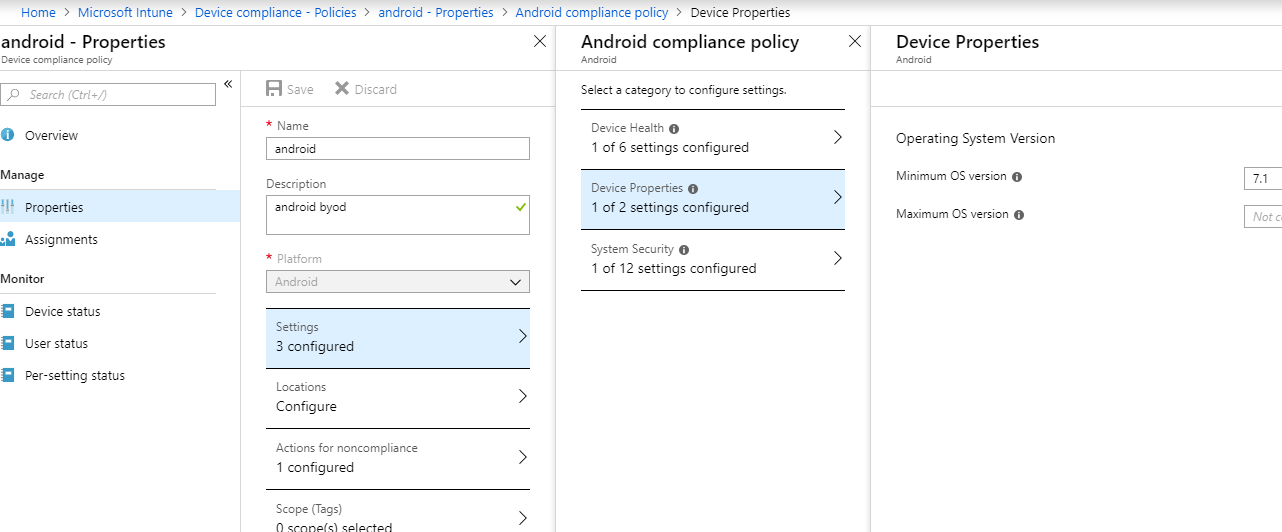
Compliance policies conditions and actions can be created based on the requirement.
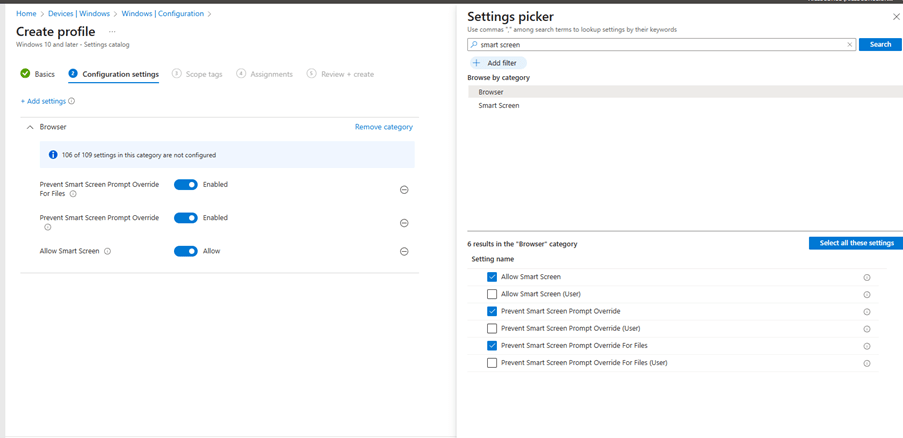
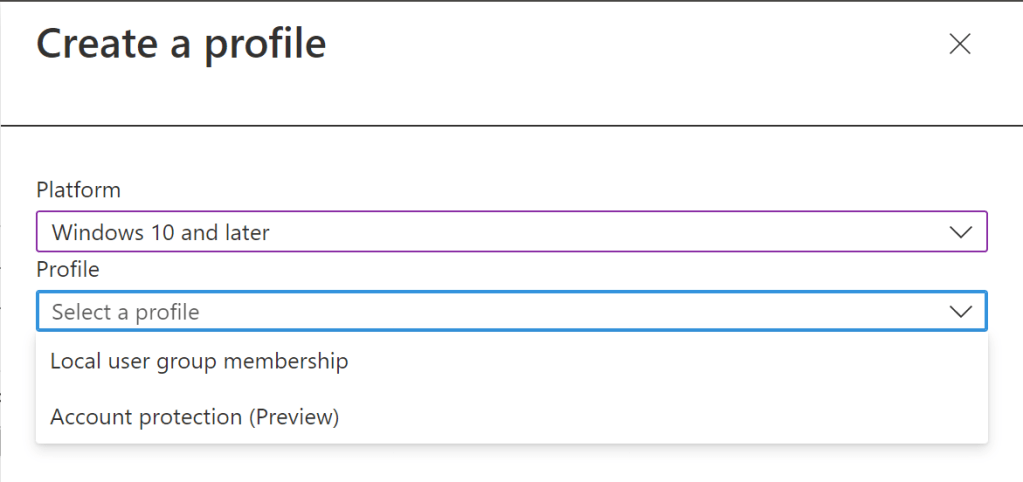
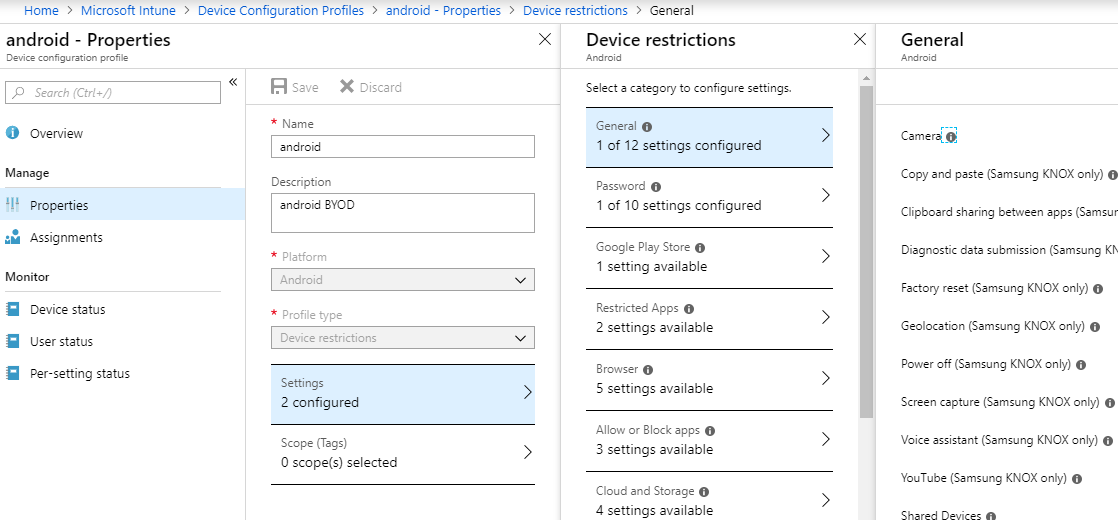
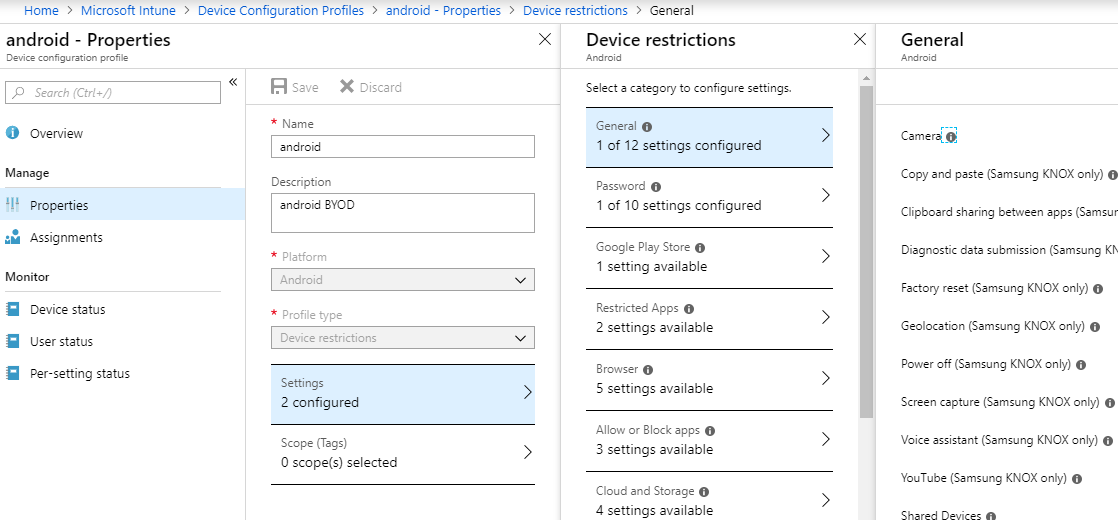
Create Configuration Policy:
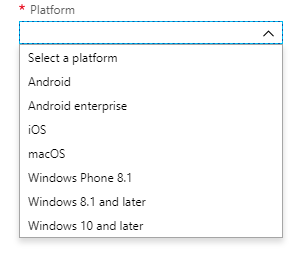
Configuration policies can be created for Android, Android Enterprise and IOS in our case , since we are focusing only on configuring the MDM for mobile devices.
Example of creating one configuration policy for Android devices and restrictions that can be applied to secure corporate data like disable screen capture, copy paste.
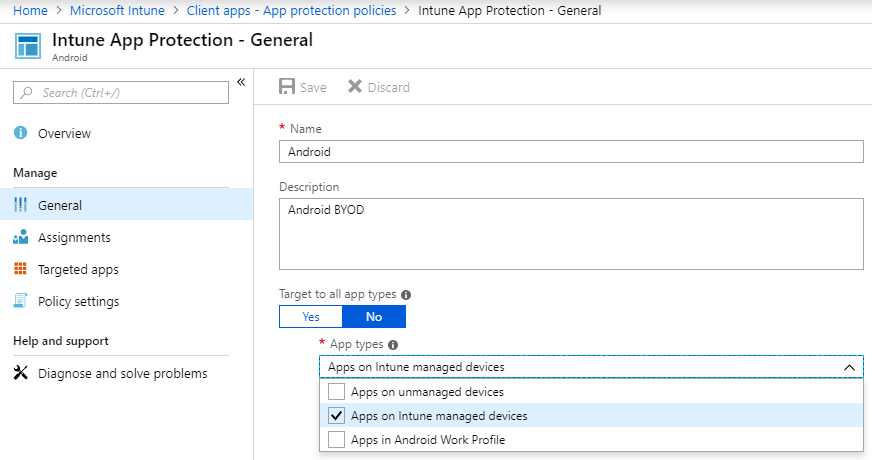
App Protection Policy:.
The app protection policy can be used to protect and enforce policy only on selective apps. This helps the admins to control only the corporate data even on BYOD devices.
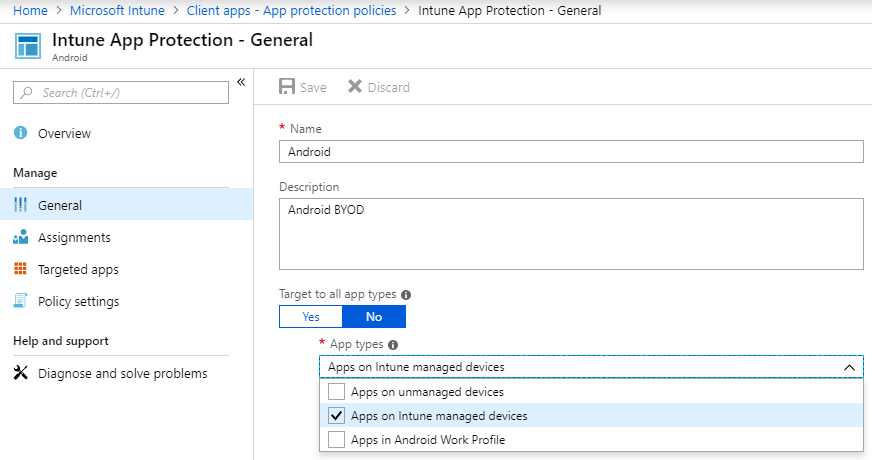
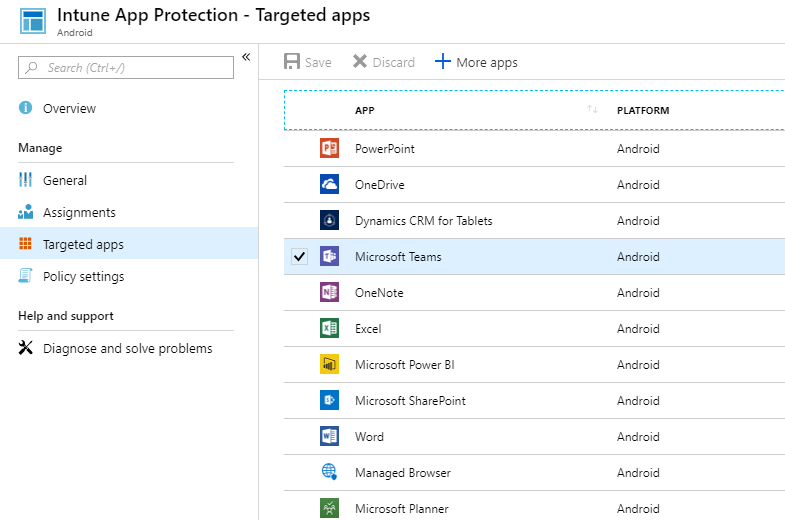
Targeted apps can be selected here we can select only required corporate apps.
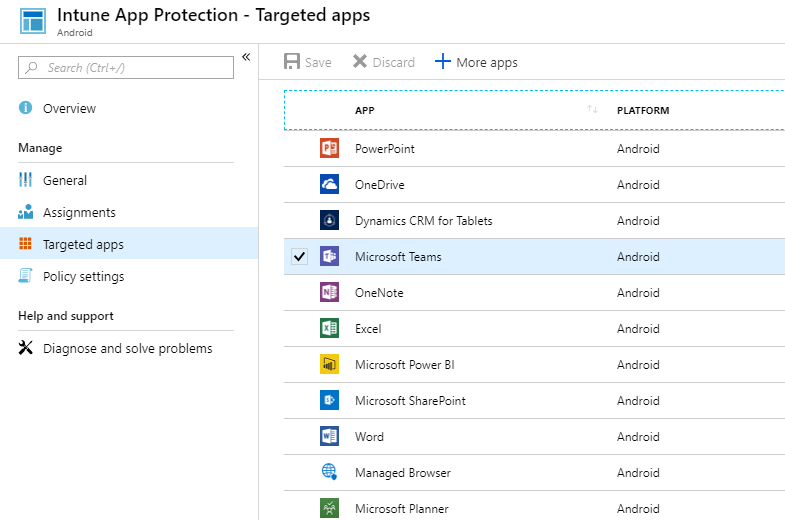
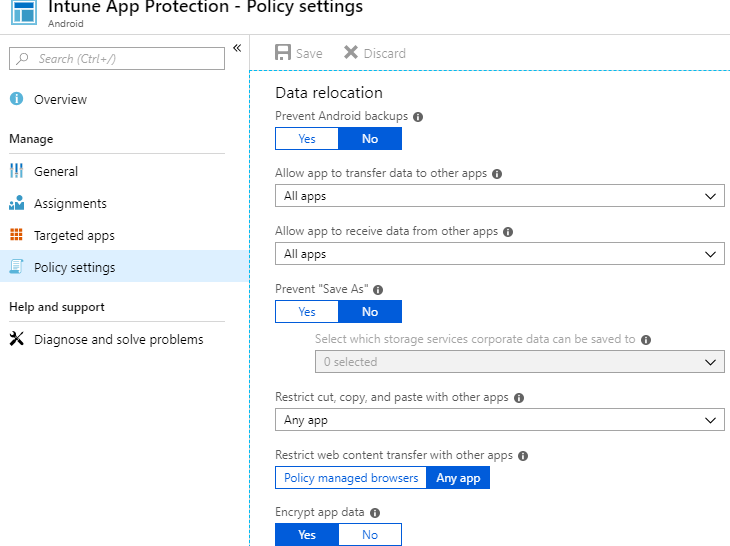
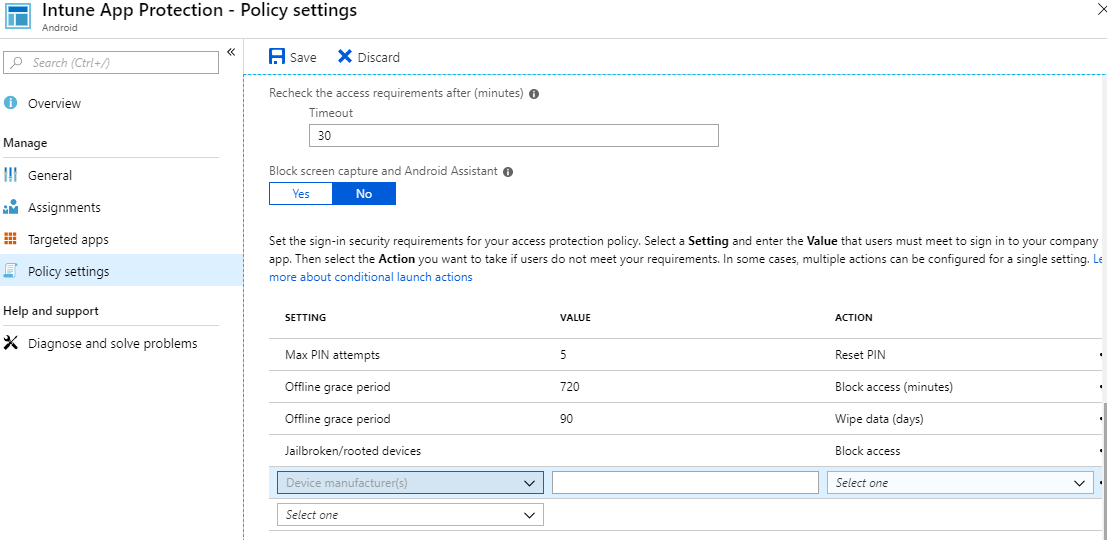
We have policy settings which can be controlled for the apps installed on the mobile phone.
Example we have an option to choose which storage can be enforced to end users to save the data. These restrictions are applicable only for the targeted apps which we have selected in the previous section.
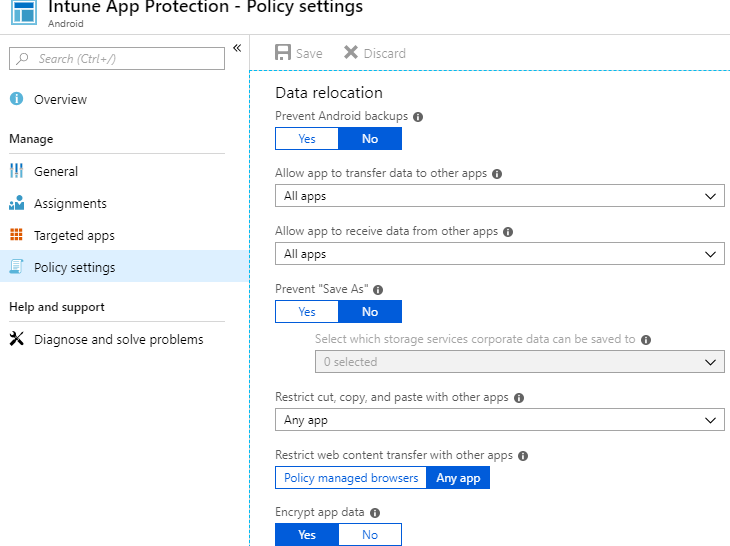
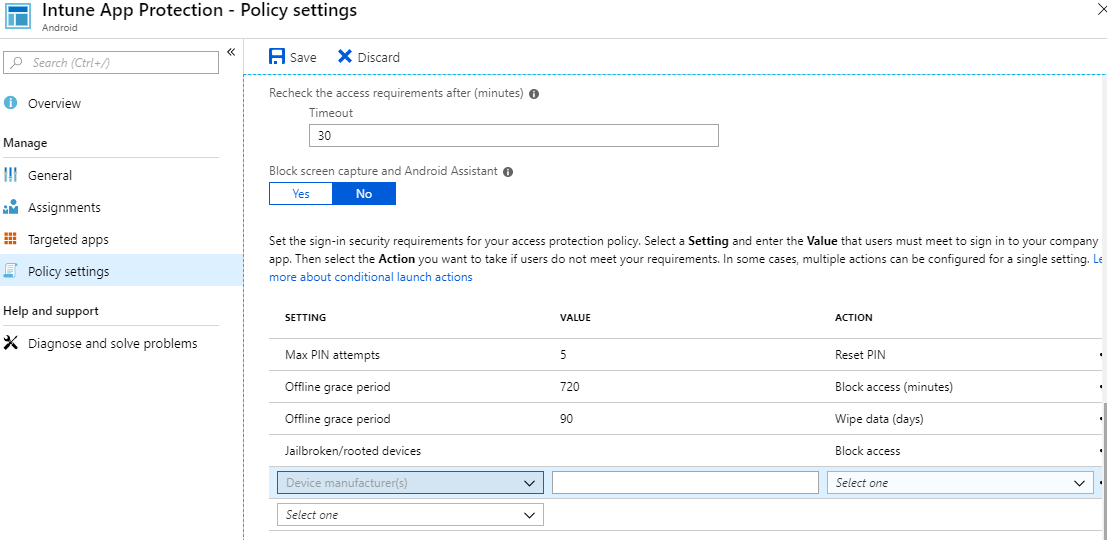
Further sign in security requirements can be controlled based on Device Manufacturers, Pin Attempts etc..,
Create Client Apps:
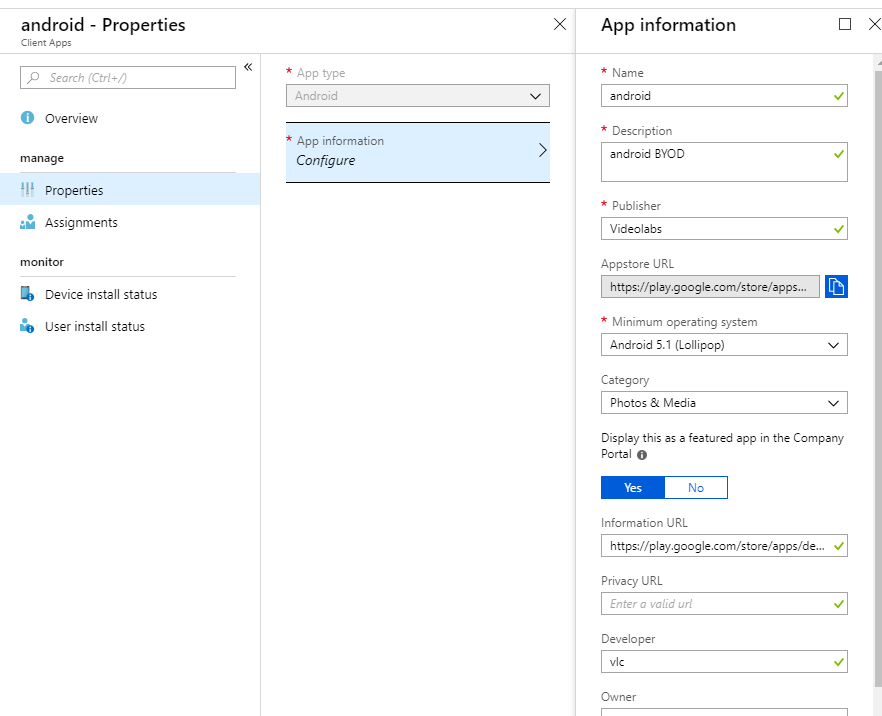
Also Intune Client apps can be assigned Android/IOS to end users through intune company portal.
Example one created for publishing VLC player in the Intune Company portal for Android Users.
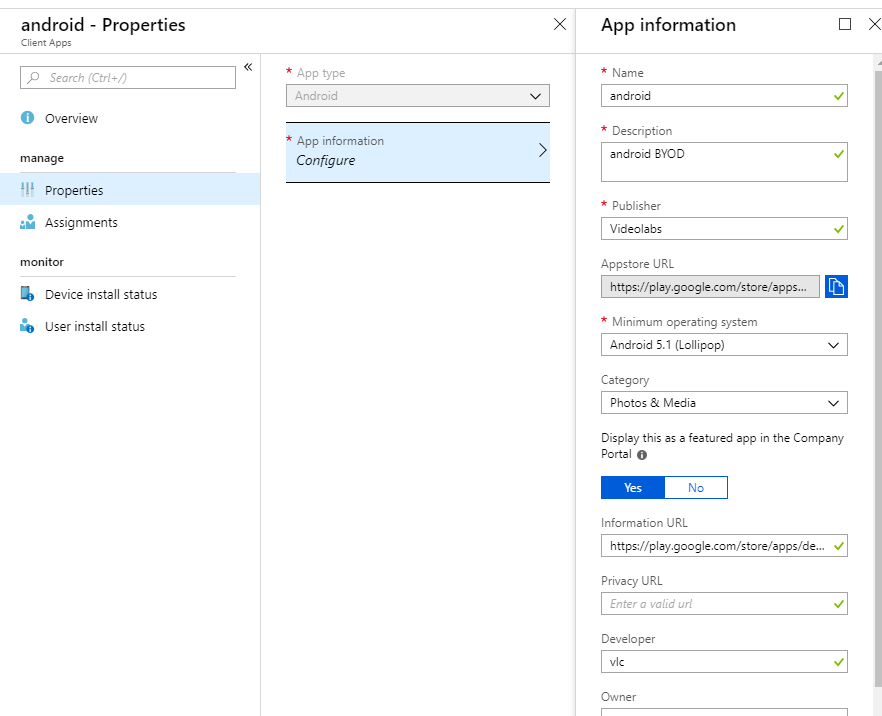
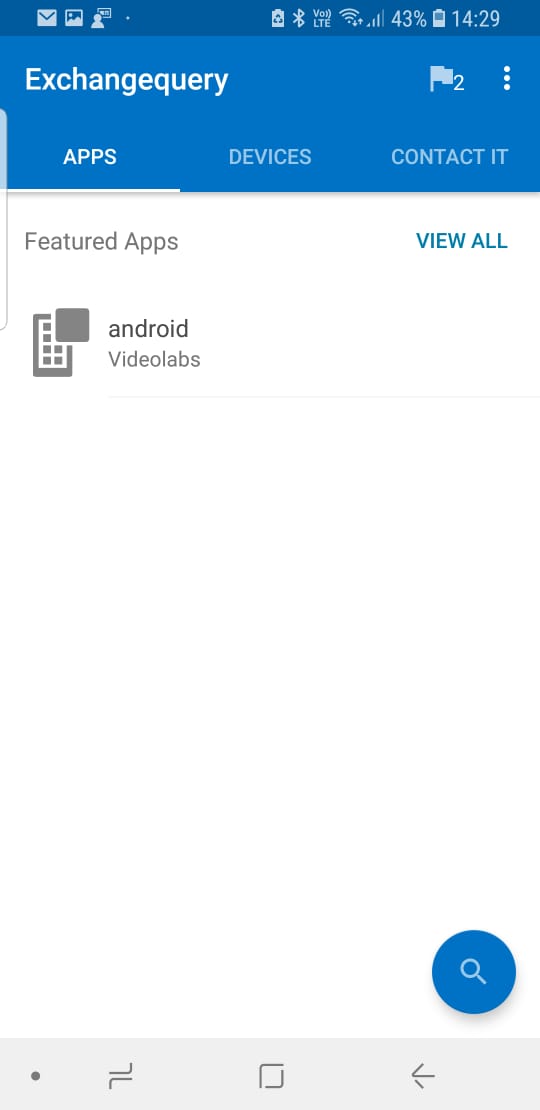
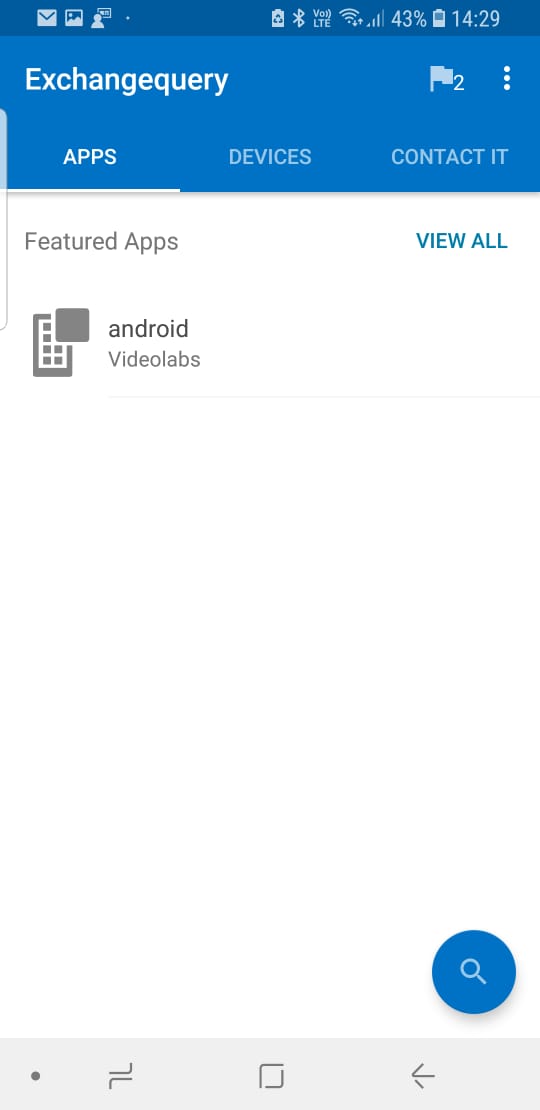
Once applied end user can see this apps from the android device from the Intune Company Portal App.
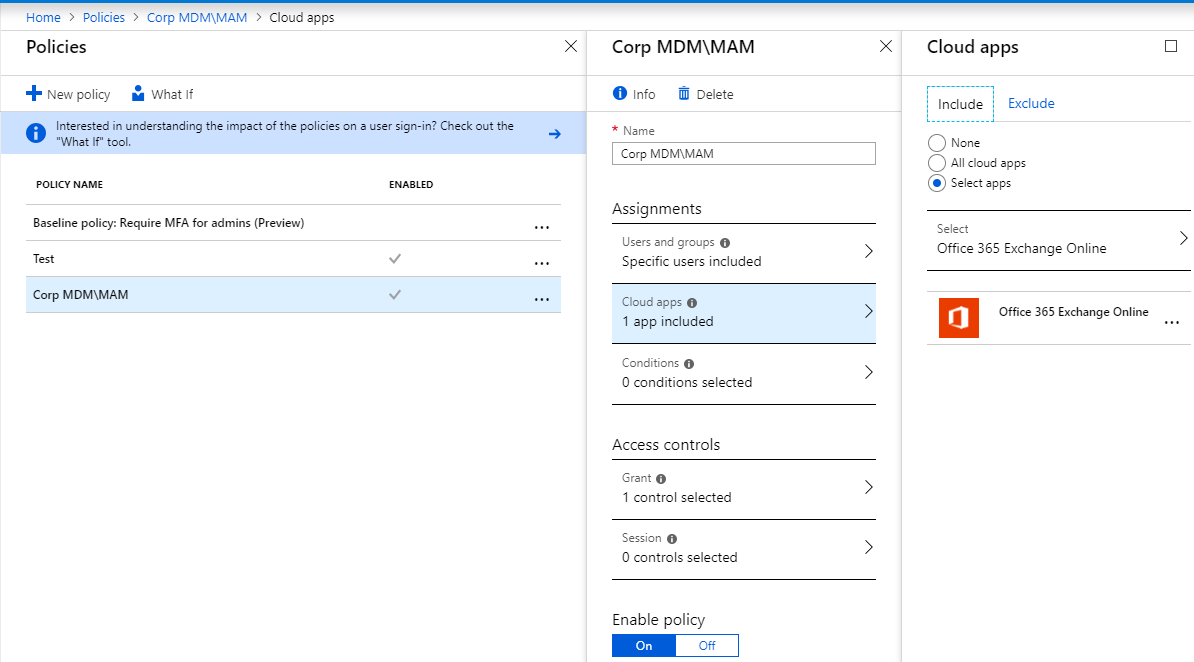
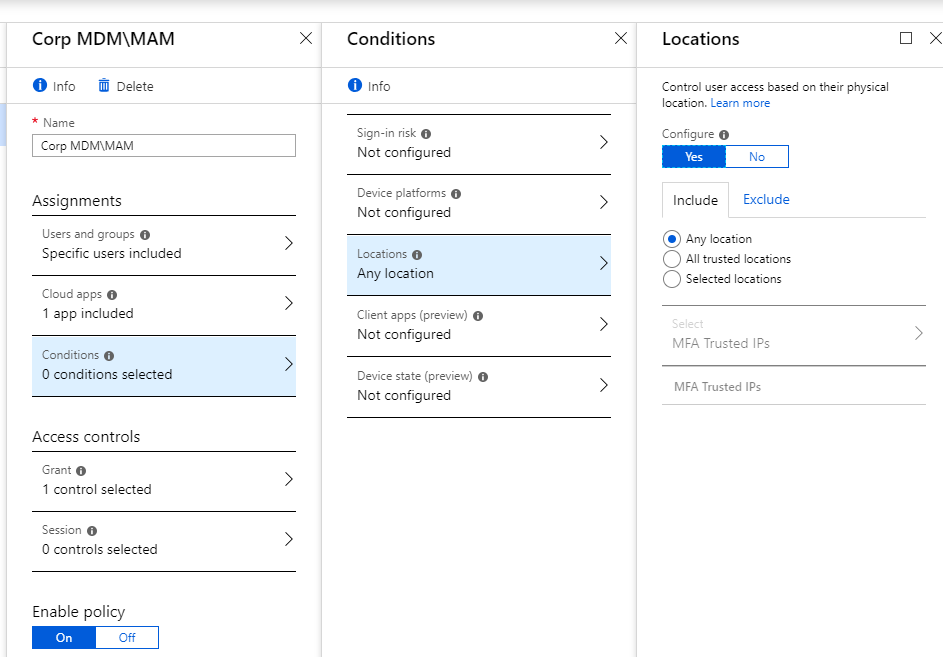
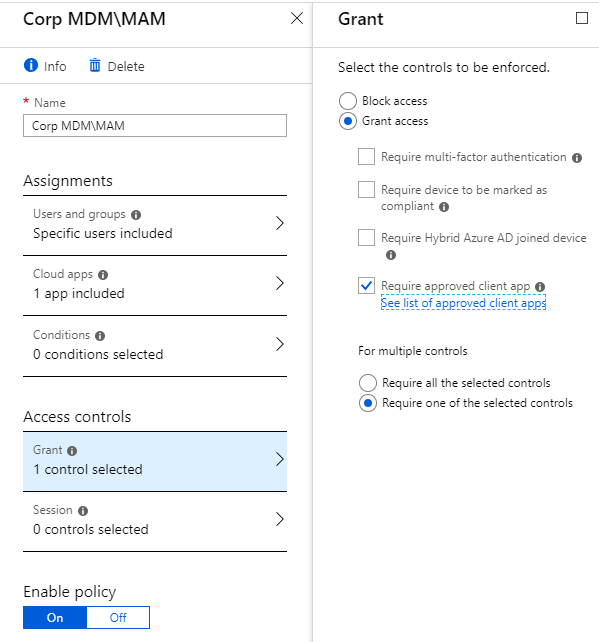
Conditional Access Policy for MDM can be created like below:
Select apps – Create one only for Exchange Online
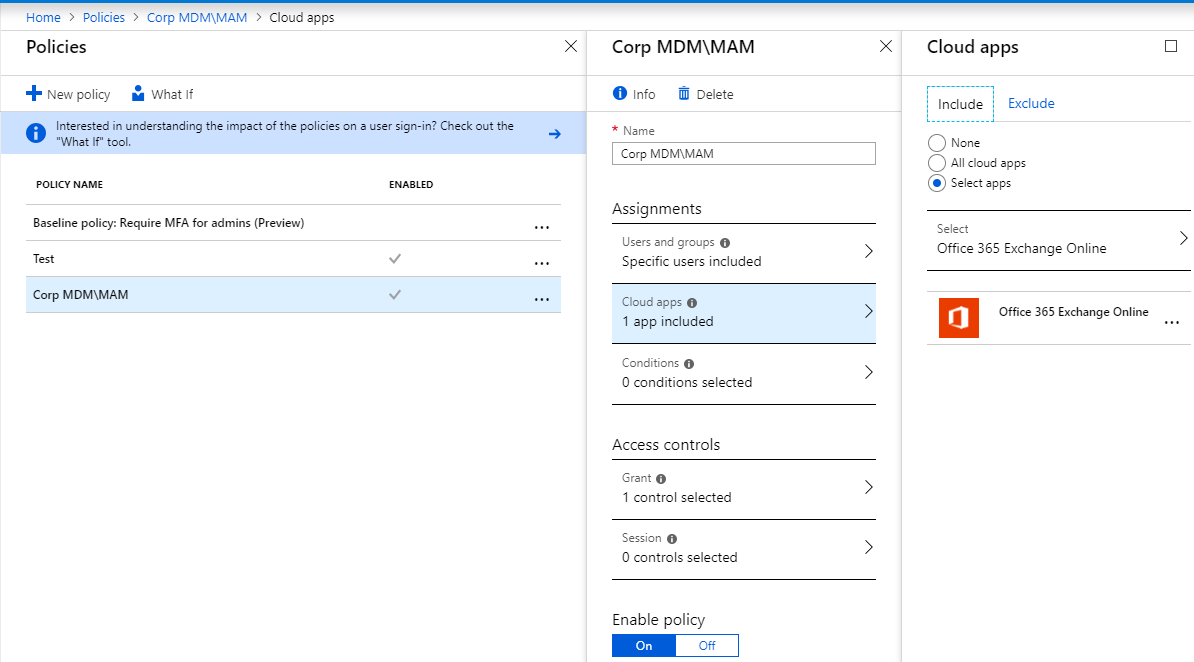
Login location can be set from where the user access can be controlled based on physical location.
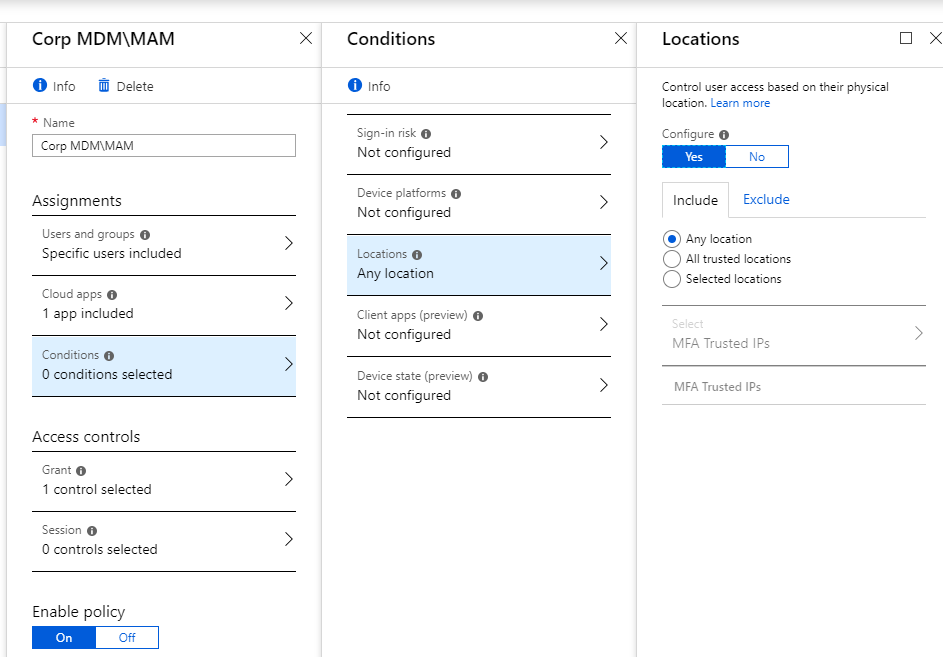
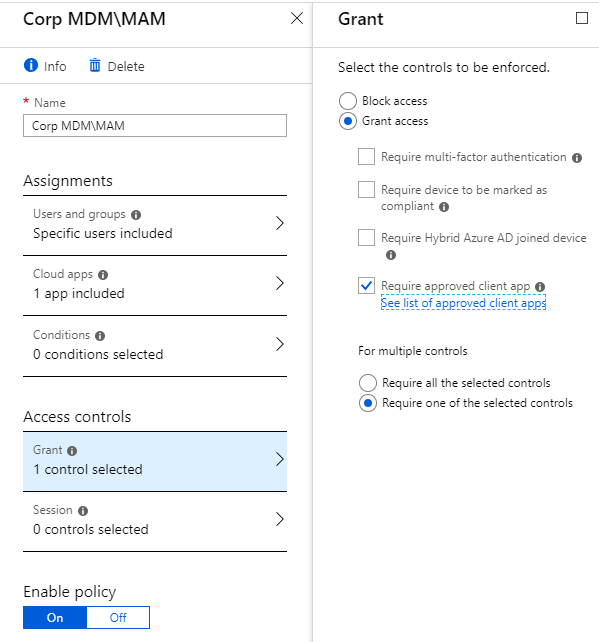
Required approved client app only can be selected.
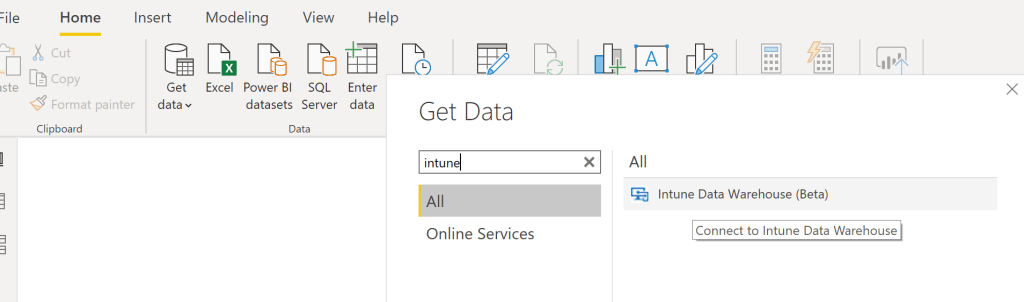
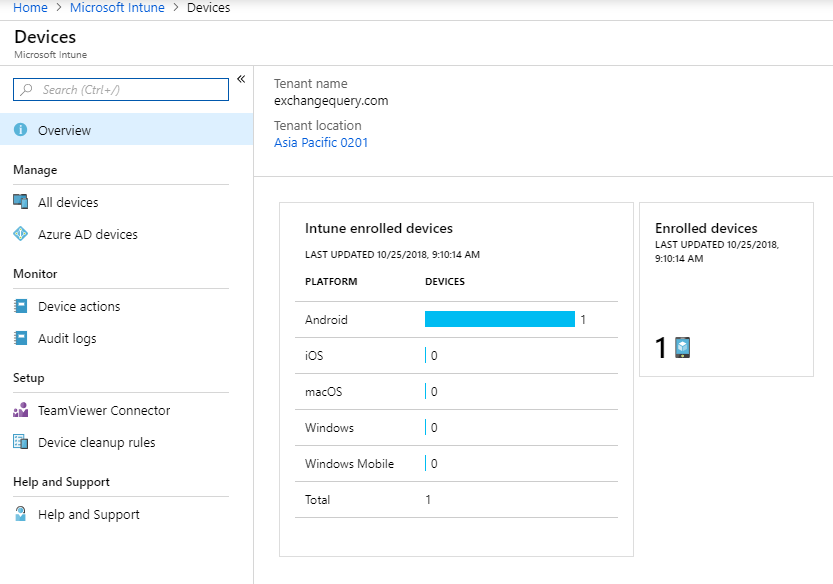
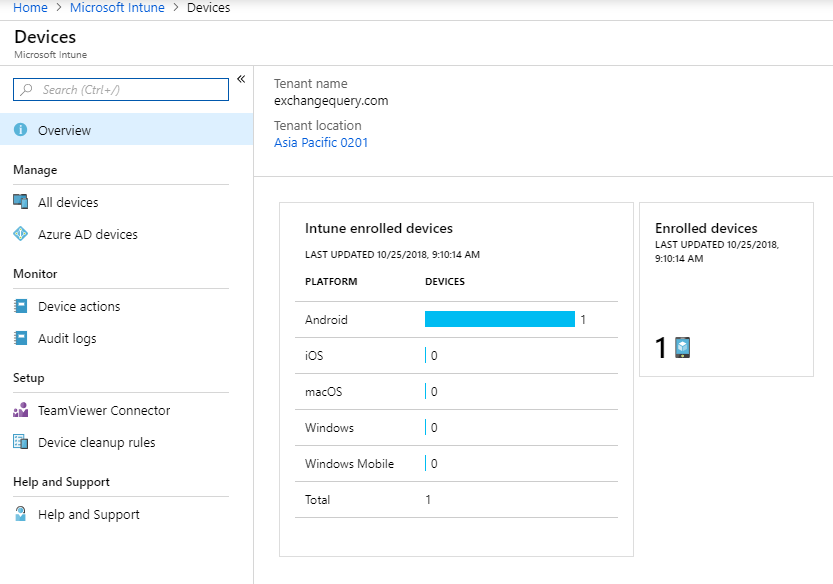
List of Intune enrolled devices can be seen.
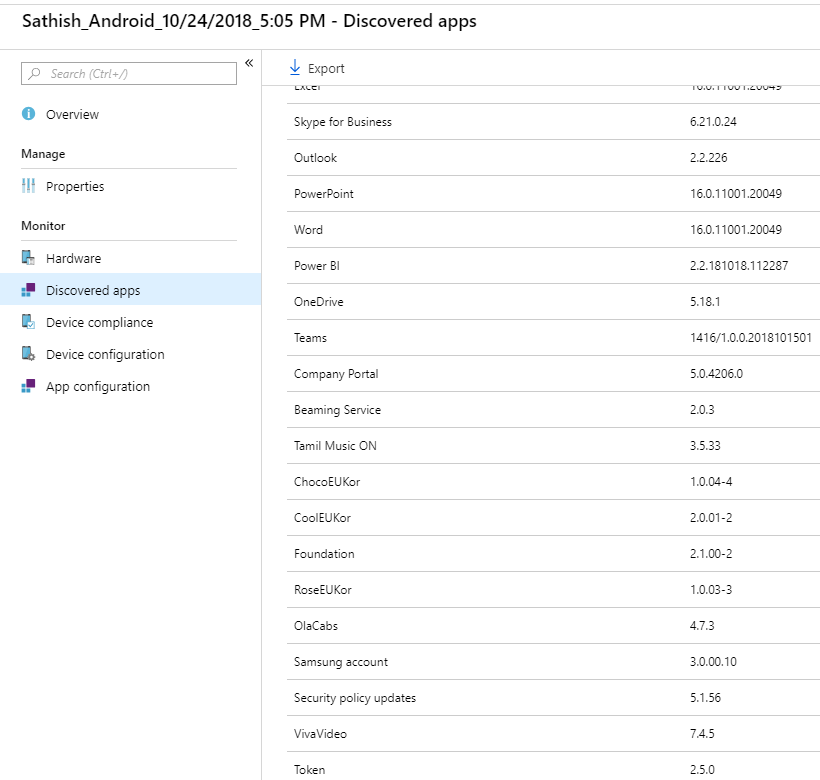
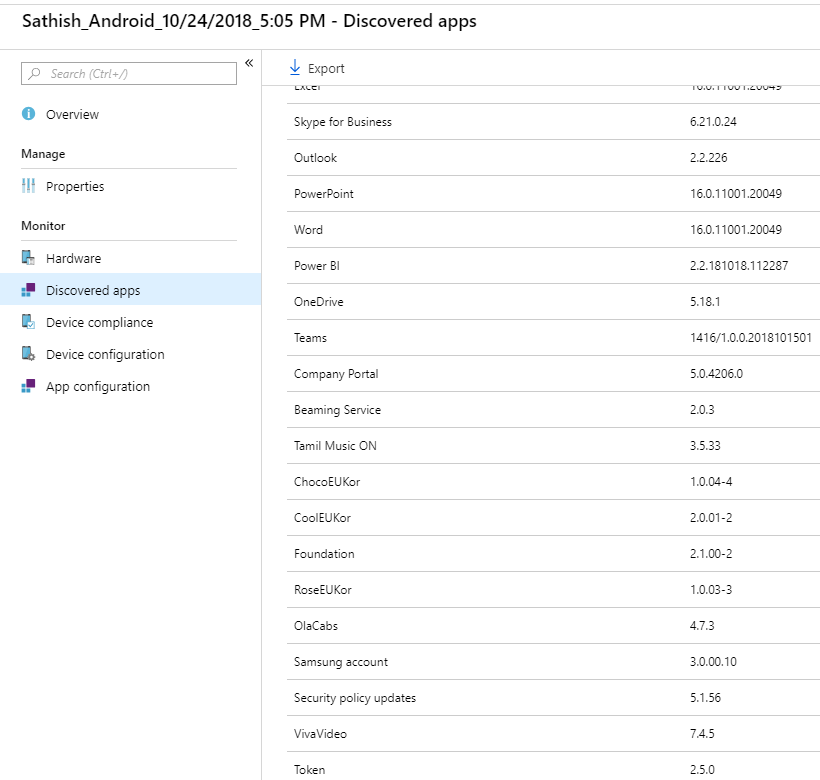
When drill down further it would show all the installed apps in the discovered apps section.
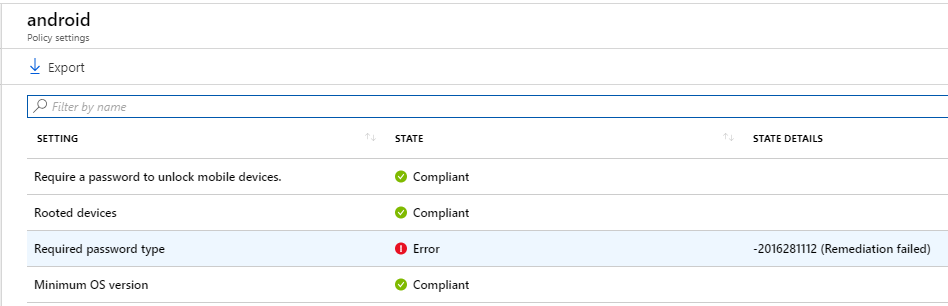
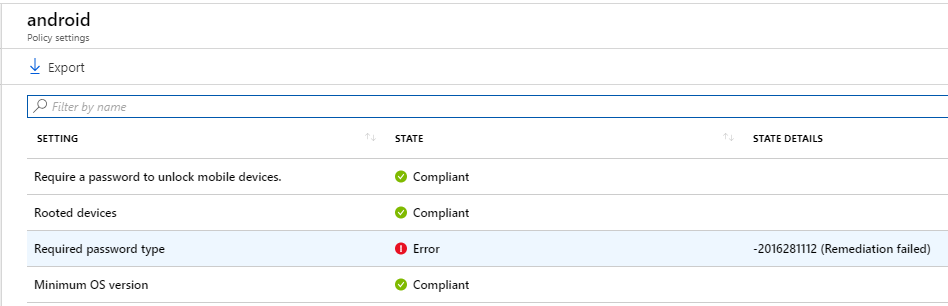
Further we can see the device compliance status. In below case my device is compliant except for the password which i did not configure as per the password policy set for Android devices.
From the client side in Android device user needs to download the company portal to access all Intune features.
- Example VLC app which we published from Client apps for end users.
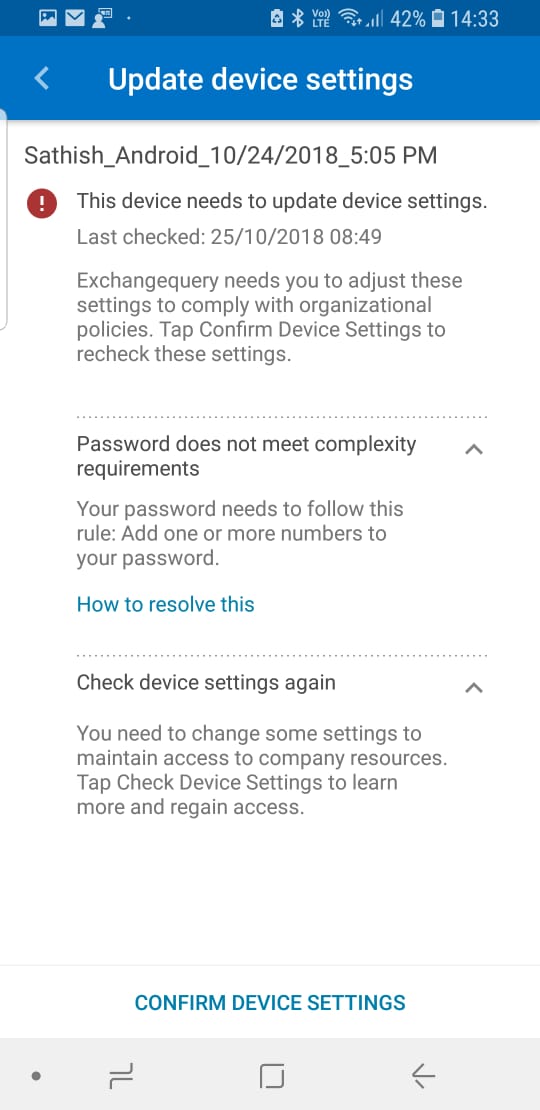
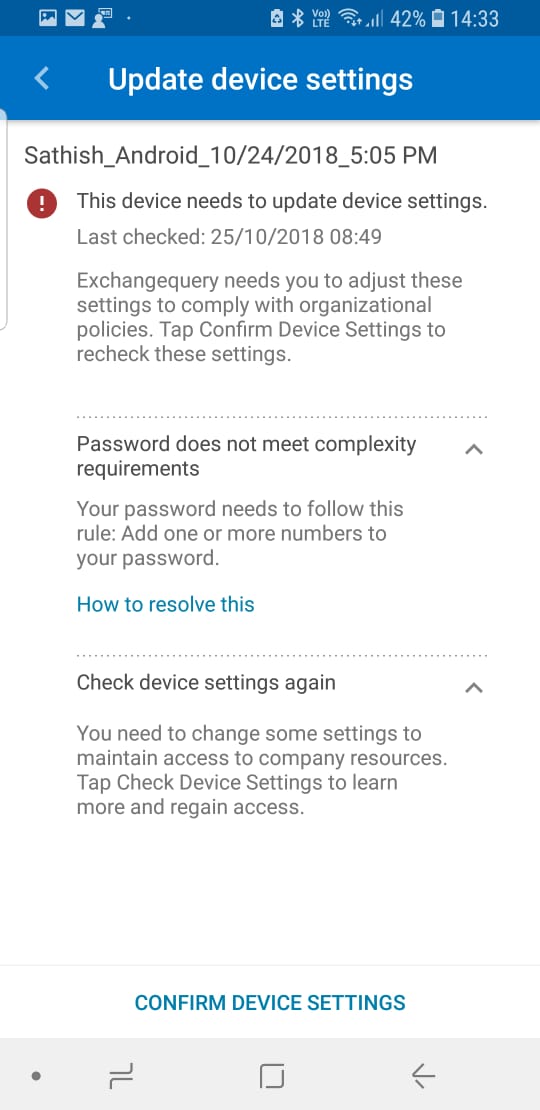
- If the device is not meeting the compliance requirements we get the alert on devices tab.
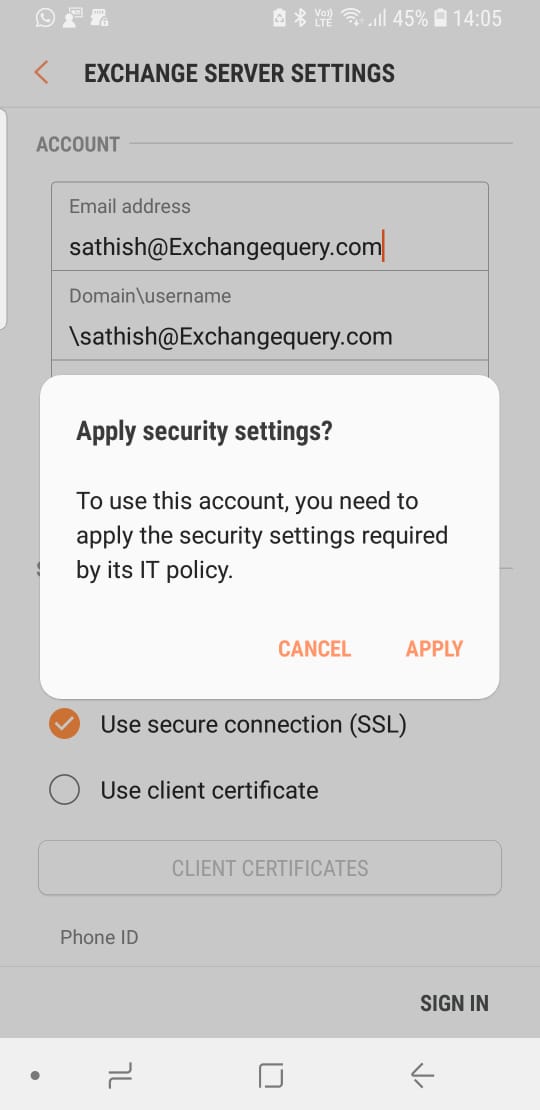
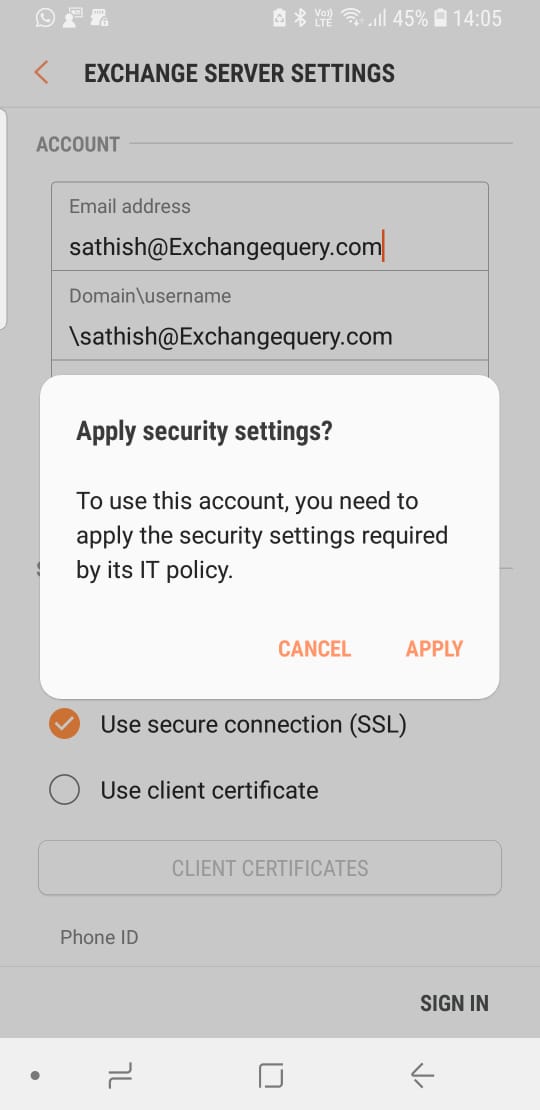
- We get the user warning when the user configures the email.
Notes:
- This blog gives an overview of how to start enrolling mobile devices through Intune for Office 365 Apps. There are more options available in intune for MDM\MAM and these have to be configured based on the requirement.
- If there are currently any MDM solution in place we need to analyze the current user experience provided to the end users and provide the same or enhance more than the current one.
- Its always recommended to test all these features in staging domain evaluate the results before moving into production
- Best recommended to roll out the MDM intune only for few pilot test users in beginning and later perform a staged roll outs based on the end user responses.
Continue reading →