Microsoft has invested a lot of new upgrades in end point security in the last few of years. We can use Intune endpoint security policies for account protection to safeguard users’ identities and accounts, as well as control device built-in group memberships. In the end point security policies we can do the account protection and we will have a look at the settings in this article
To get started navigate to endpoint security and click on account protection. Here we have the opportunity to create an account protection policy.

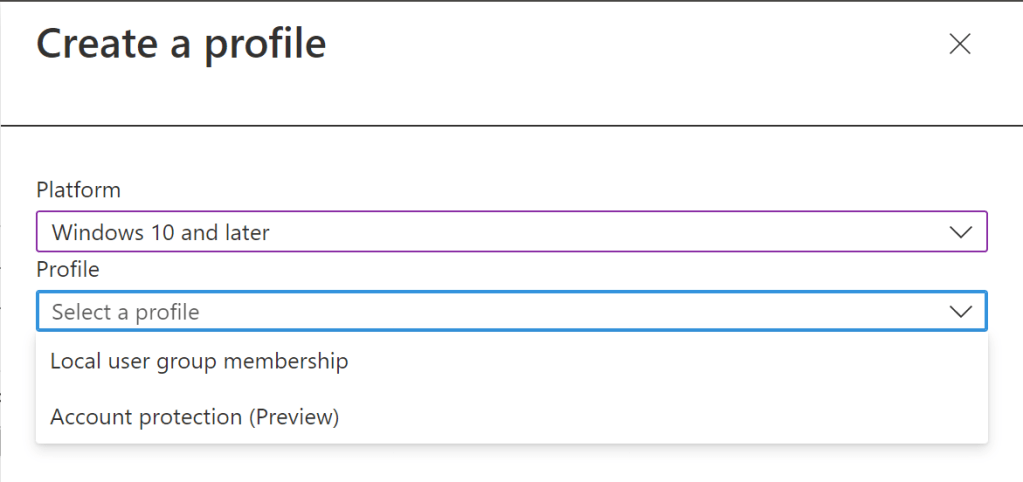
When creating the new policy at the time of writing this blog we have option to create the policy for the platform Windows 10 and later. And the profile is targeted for two profiles local user group membership or account protection which is in preview state at this moment.
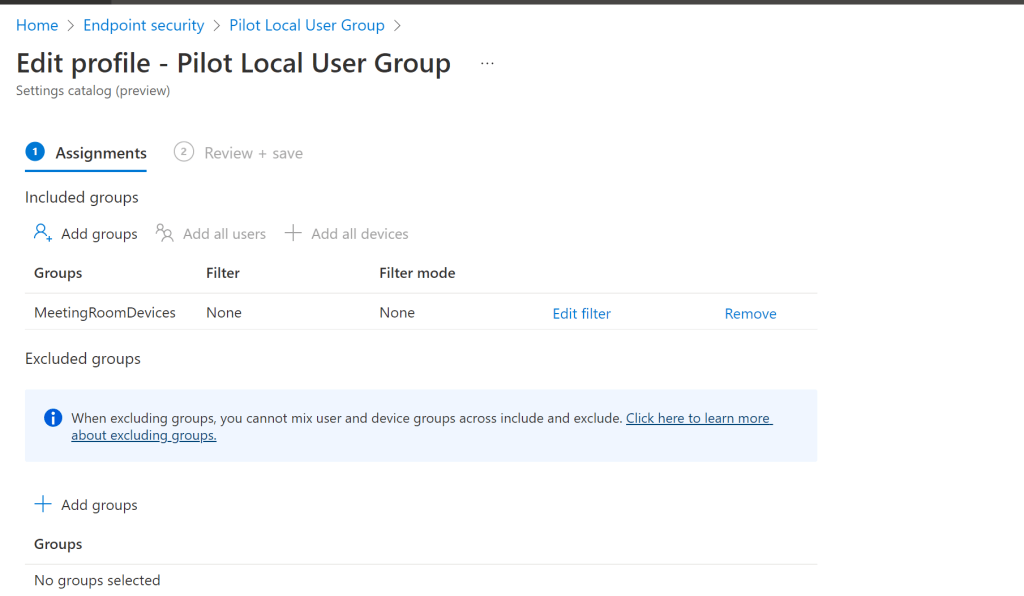
When creating for local user group we have the below options where we can select administrators and other set of user groups as we see below.

And in the group or user section place we have the possibility to add ,remove or replace the users. And inturn we have an option to select the users or groups from the selection pane. The great part is we will be able to choose the directory synched objects in the selected criteria list. This is of great benefit for instance managing a user access to workstations from the local RBAC instance for example.

In our example have chosen one directory synched group from local AD and directly created Azure Object to see the differences.

In the same way a separate profile has been created for account protection. At the time of writing this blog could see that we can protect the below configuration settings with the account protection. For instance we can block windows hello for business. If we enable this policy setting, the device does not provision Windows Hello for Business for any user.
Furthermore there are more options like to enable to use security keys for sign in and turn on credential guard. Credential Guard uses Windows Hypervisor to provide protections, which requires Secure Boot and DMA protections to function, which require hardware support. because they are providing kernel DMA support. This setting will only successfully enable if the hardware requirements are met. These settings can be more beneficial for shared computers and for example meeting room devices as well.

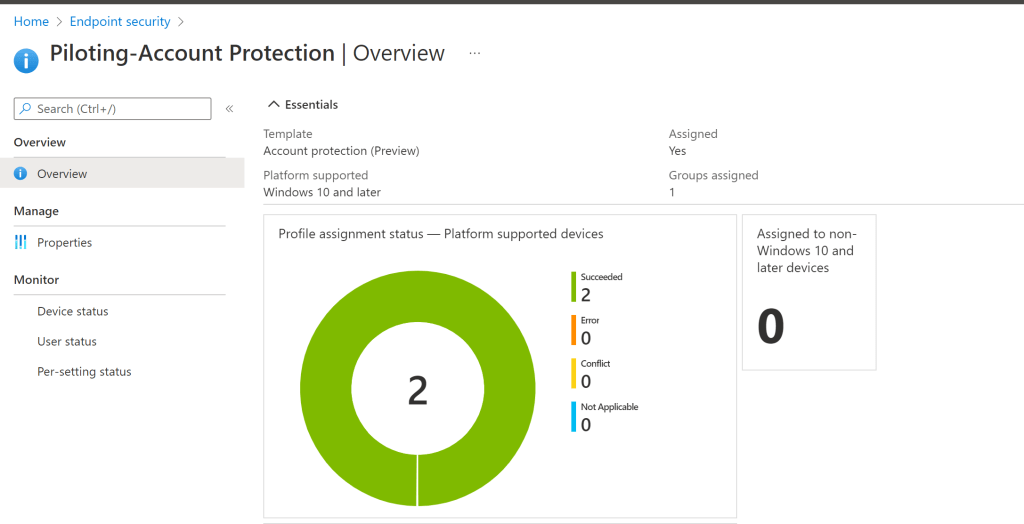
And after a successful assignment of these profiles we can see the status as successful like example below. In our case we have targeted this to 2 devices and they are successful.
Moreover we also can have a look at the per setting status.

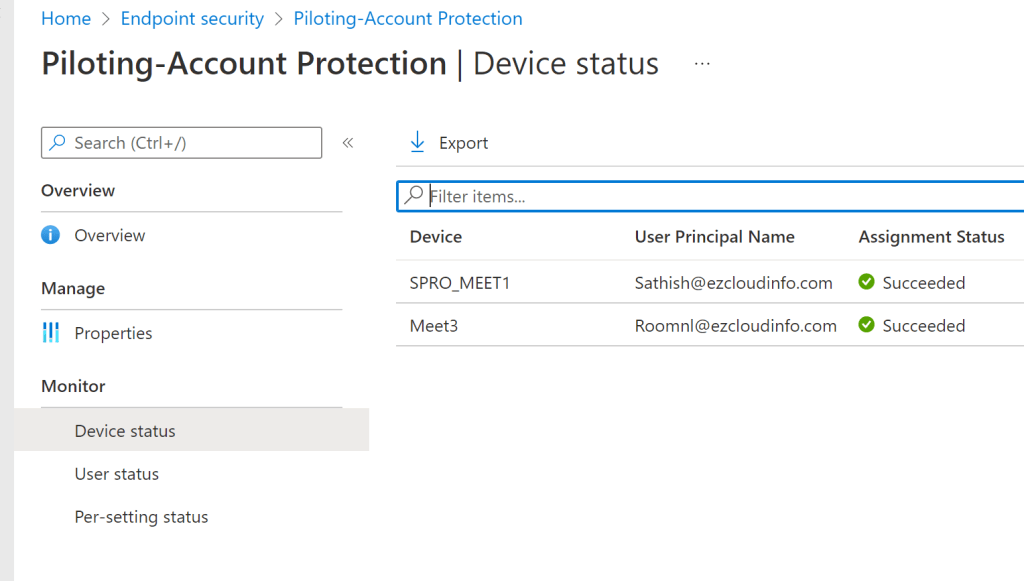
And in the user status we see that the policy has been successfully applied to the accounts that is using these devices. Im still not clear about how it picked up the UPN without specifying , however will update this section more when i get more details on the same.

In the device status we can see that two devices have successfully been applied and the associated account have also been picked up as we discussed in the previous screenshot.
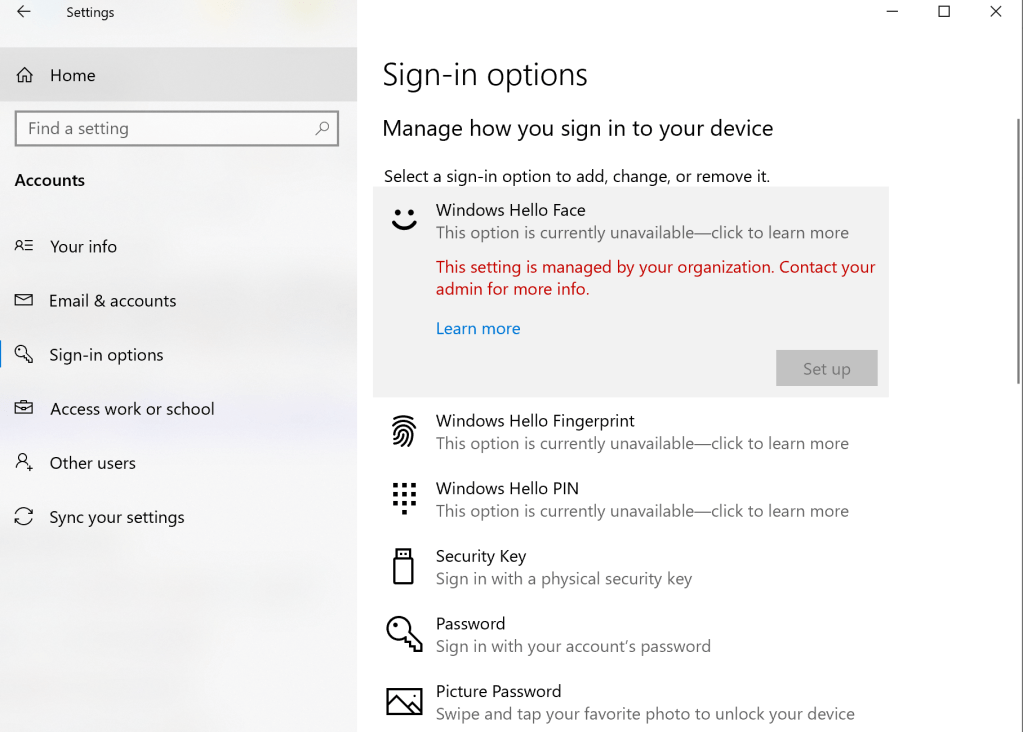
And to see if the policy has been successfully applied logged into one of the windows device that has targeted this account protection profile. Attempted to enable windows hello face and it did not allow me further to setup because of the policy enforcement we have done from the profile.
And for local user membership testing in my scenario there were 2 devices targeted. 1 out of 2 devices did not get the profile successfully enabled. On the failed device I got the error code 65000. Will look into this failure and will post a separate blog on this part.

When looking into one of the device where the profile got successfully enabled we can see that the group configuration is succeeded.

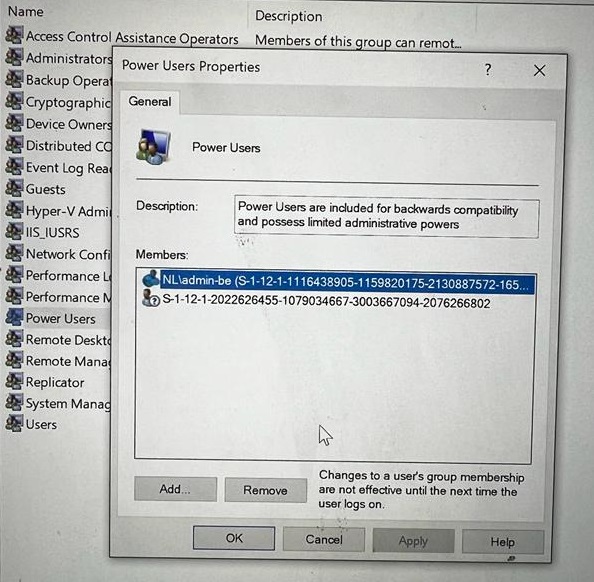
Having seen this successful configurations on the Intune portal. Now lets see the reality if the targeted users were really added to the Local Admin and the power users group.
Into the Power User Group – We see that the local Synchronized AD account is added successfully
The other one with SID is most probably the cloud only account which we attempted.
The same case is also applicable with the local administrator group. We also see that the local Synchronized AD account is added successfully
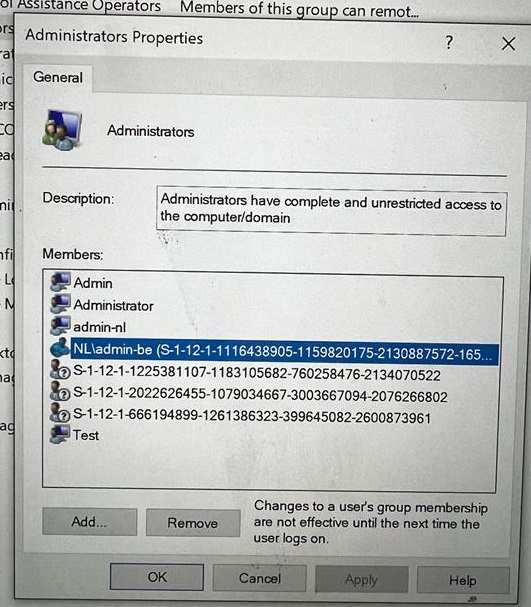
This is a great way to manage the local admin access for applications that is running on windows devices in KIOSK mode. For Example we can take an example of room systems where only specific local admin accounts can be added where they can manage the room systems.
The security settings on devices, we can use Intune endpoint security policies. One or more profiles are supported by each endpoint security policy. Account protection policies assists us in safeguarding your users’ identities and accounts. The Windows Hello and Credential Guard settings are covered by the account protection policy, which is part of Windows identity and access management.


Leave a comment