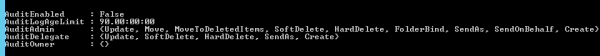
This document outlines the steps to renew the SSL certificate for ADFS claims providers federation metadata URL
1) To take the application ID and the certificate hash run the below command.
netsh http show sslcert
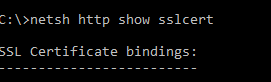
copy only application id value. This we require for the certificate renewal. Better to take a copy of this results.
2) Run this command to see the ADFS listners
netsh http show urlacl
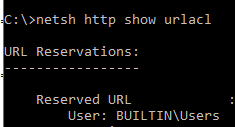
This is just to take a copy of the ACL url’s before the certificate renewal. This part is so sensitive because ADFS will have some URL reservations in the HTTP.SYS. This will help us just in case if we face any issues after the certificate renewal.
3) Delete the old certificates –
$Command = “http delete sslcert hostnameport=adfs.exchangequery.com:443”
$Command | netsh
$Command = “http delete sslcert hostnameport=adfs.exchangequery.com:49443”
$Command | netsh
$Command = “http delete sslcert hostnameport=localhost:443”
$Command | netsh
$Command = “http delete sslcert hostnameport=EnterpriseRegistration.exchangequery.com:443”
$Command | netsh
4) Delete the old hostIP and port entries:
$Command = “http delete sslcert hostnameport=0.0.0.0:443”
$Command | netsh
5) Now we can add the new certificates:
Prerequisite:
Take the APP id which was noted down in the step 1
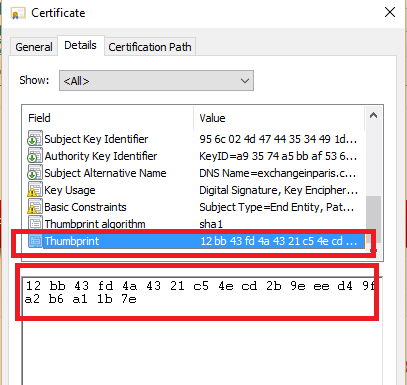
Take the certificate Hash – This can be taken from the new certificate thumbprint
example below – remove all the spaces and copy the new certificate hash value.
# APP ID
$guid = “paste the appid here”
# Cert Hash
$certhash = “paste the certificatethumbprint”
To renew actual metadata URL:
$hostnameport = “adfs.exchangequery.com:443”
$Command = “http add sslcert hostnameport=$hostnameport certhash=$certhash appid={$guid} certstorename=MY sslctlstorename=AdfsTrustedDevices clientcertnegotiation=disable”
$Command | netsh
To renew localhost:
$hostnameport = “localhost:443”
$Command = “http add sslcert hostnameport=$hostnameport certhash=$certhash appid={$guid} certstorename=MY sslctlstorename=AdfsTrustedDevices clientcertnegotiation=disable”
$Command | netsh
To renew Device Registrations:
$hostnameport = “adfs.exchangequery.com:49443”
$Command = “http add sslcert hostnameport=$hostnameport certhash=$certhash appid={$guid} certstorename=MY clientcertnegotiation=enable”
$Command | netsh
The above is required because Changes were made in ADFS on Windows Server 2012 R2 to support Device registration and happens on port 49443.
$hostnameport = “EnterpriseRegistration.exchangequery.com:443”
$Command = “http add sslcert hostnameport=$hostnameport certhash=$certhash appid={$guid} certstorename=MY sslctlstorename=AdfsTrustedDevices clientcertnegotiation=disable”
$Command | netsh
The above is also required for device registration service.
Hope this helps.