Maintaining the signature format uniformly for all the users is really a difficult task.Also the signature format will be changing on department, user and job role basis.
At times there might be a requirement to modify the signatures for departments based on events as well.
As an admin it will be very difficult if you are not having any centralized signature system for the messaging systems.
Out of the available signature applications in the market i always prefer Exclaimer based on their support and options available in their product. In this article we will have a look at configuring the Exclaimer Signature and run through some of the options available in their product.
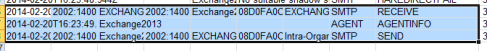
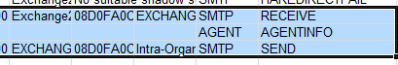
The installation and configurations are very simple since it is just a transport agent which will be triggered in the categorizer part and signature will be applied. So this application has to be installed on a server where the transport categorization takes place.
In Exchange 2010 this application needs to be installed on the Hub Transport server
In exchange 2013 & 2016 it has to be installed on Mailbox servers.
One thing we need to make sure is that it has to be installed on all the HUB servers if its exchange 2010 and all the mailbox servers if its exchange 2013 & 2016. This is because the Mail-routing can happen in any of the available transport services and this application needs to be there to trigger in the categorization part.
The installation is pretty simple and straight forward which is very easy .Just need to download the application and install them.
The application can be downloaded from below url
https://www.exclaimer.ae/signature-manager-exchange-edition/download

We have the option to keep a backup of the previous configurations which will be easier to revert.
There is option called remote deployment where we need to configure a shared folder for the exclaimer images, configuration files to be stored in a common location so that all the transport servers can be updated without any delay.

Below are the options available for the sent items configuration which are pretty much easier to understand.
It has a temporary file folder where it processes all the signature as a cache before applying them. You can specify a drive on your own.

After a successful installation we will get a screen as below
We can have multiple signature policies based on department, Organizational Unit and apply to respective ones.

So this signature pulls all the information like Name, Company, Phone Number ..etc from the information present in the mailbox.
So all we need to do is to create a new policy choose and apply the desired values as below from the new created template

We have an option to change the element behavior , layouts as well.

Note: We need to make sure that all the user information like Name, Phone Number, Company are updated. Only then it will update the information from the User object and reflecting in the signature. If the field is not updated then the information will show empty.
The signature can be customized further as well by adding an image, hyperlink to the attached image to them. All kinds of alignments, layouts can be done for the same.

Moreover we have an option to edit the source code of the HTML which is a great amazing feature. By having this option we can customize the signature templates of our own according to the requirement.

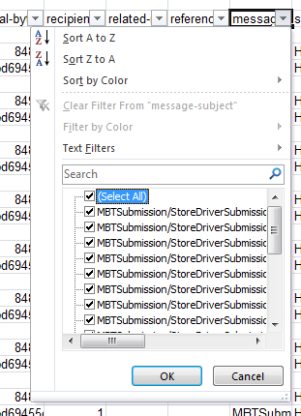
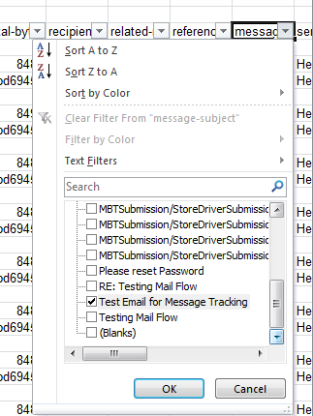
There are multiple options available to apply signature based on the requirement.
An example below.

Also we can set exceptions for few users who does not like to have this automated signature policy.We have an option to apply the signature only on a specific date and after that it will be disabled automatically.
There are more features and options available to explore on this product.
Overall we will get a very good support, latest updates, very simple installation configuration and more features available to customize with this exclaimer application. And so far with all versions of exchange this product has been always a bread and butter and haven’t caused any issues in terms of considering them as a third party Transport Agent.
Thanks & Regards
Sathish Veerapandian
MVP – Office Servers & Services