In this article lets have a look at troubleshooting POP and IMAP connectivity issues in Exchange 2013.
First lets have a basic requirements to check what are the features and things that needs to be enabled in-order for these services to work.
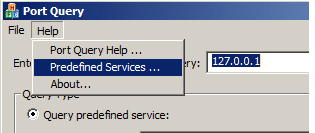
What ports should be used by the clients for each configuration : –
Port 25 for SMTP with or without TLS, anonymous authentication; (Outgoing)
Port 587 for SMTP with TLS; (Outgoing)
Port 143 for IMAP without TLS (Incoming);
Port 993 for IMAP with SSL/TLS (Incoming)
Port 110 for POP3 without TLS (Incoming);
Port 995 for POP3 with SSL/TLS (Incoming);
Ensure that all the required ports are open in your firewall accoding to the configuration you have ( with or without TLS). Probably we can do a telnet from externally and see if we get a proper banner.
For POP – Telnet domainname 110
FOr IMAP – Telnet domainname 143
For TLS to work do we need to install any certificates on the servers : –
You should create certificate including your CAS server FQDN and Mailbox FQDN as the SAN name. It should not be self-signed certificate. You should get it from an internal CA or a public CA. Then assign the services SMTP, POP3, IMAP and IIS to this certificate only then it will work.
Do we need to configure anything on the server for POP and IMAP Authentication : –
For Authentication type for POP and IMAP Services, we can choose to use plaintextlogin or securelogin. You can refer to http://technet.microsoft.com/library/aa997188(v=exchg.141).aspx. It defines how the application provide the username and password to do authentication.
Below things can also be checked for Troubleshooting POP and IMAP issues : –
We Can run Test-PopConnectivity and see the results
We Can run Test-imapconnectivity and see the results
Use the remote connectivity analyser for IMAP and POP and see the results
Run the below commands to see the POP and IMAP settings
Get-POPSettings -Server CASservername
Get-IMAPSettings -Server CASservername
Restart your POP3 service and see the results
Check if your POP3 service have valid certificate assigned
Run Get-ExchangeCertificate and see if the certificates are assigned for POP and IMAP services.
Check your ports config and ensure they are correct
Port 110 for POP3 without TLS;
Port 995 for POP3 with SSL;
If you have configured POP and IMAP with either SSL or TLS then a valid certificate should be configured for the same to respond to SSL or TLS(depends upon what type you choose)
Check the incoming and outgoing mail server in Outlook settings
We can enable the trace log and open the log in the location.
Please refer to http://technet.microsoft.com/en-us/library/aa997690(v=exchg.141).aspx to set the location and enable the log.
Thanks
Sathish Veerapandian
MVP – Exchange Server