It’s always difficult to protect sensitive emails being leaked out from any organization. In order to avoid this there are few things that can be blocked on the global settings from the server end.
If we have the auto forwarding and autoreply option enabled on the default remote domain then any users can create an external contact in his local outlook profile and then he can forward all his emails to his external ids. Here is the possibility again where sensitive data being leaked out from organization.
The default remote domain will have autoforward and autoreply disabled . That is the recommended configuration.
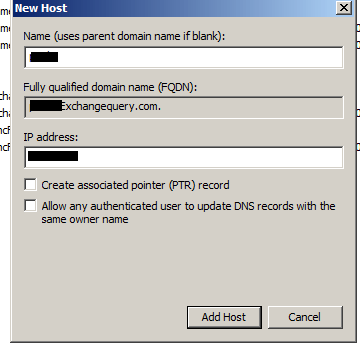
We need to disable the autoforwarding, autoreply option in the default remote domain. If in case if we are forwarding any emails to trusted partners or vendors through any application we can specifically create a custom remote domain for them and enable auto forwarding for that particular remote domain alone. By doing this no end users will be able to redirect, forward or forwardas attachment their internal emails to their external ID’s.
We can check that by running the below command
Get-RemoteDomain | ft Auto*
If it is enabled run the below commands to disable them
Set-RemoteDomain -Identity default -AutoForwardEnabled $false Set-RemoteDomain -Identity default -Autoreplyenabled $false
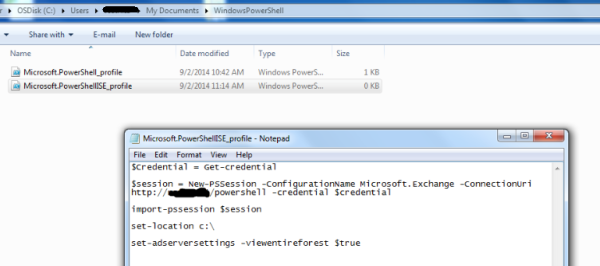
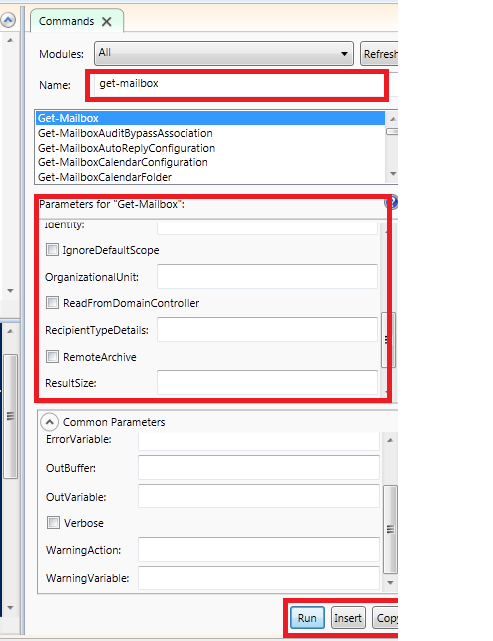
Recently I was looking for a solution for this kind of issue and came up with an idea of a script that can be used to pull out users who have redirect, forward or forwardas attachment options enabled in their outlook rules.
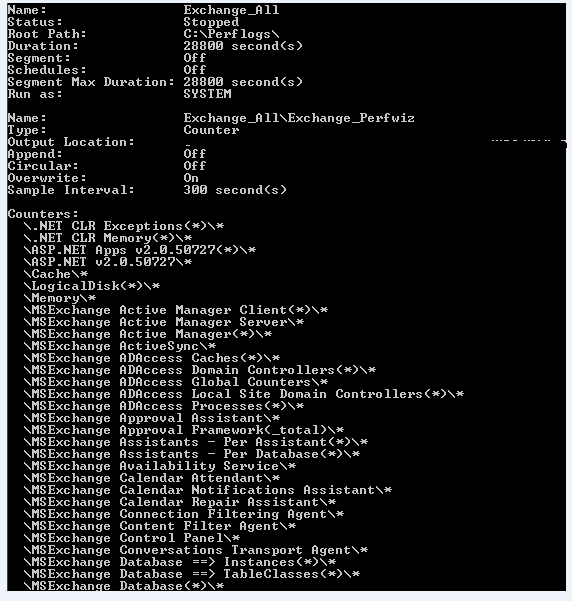
I have created a script which can be used to pull out this kind of information. The below script will run on all mailboxes in entire organization and will pull out users who have external rules set, and then it will send an email to administrator in CSV format by which he can see who all has this option enabled.
***************************************************
Set-Adserversettings -viewentireforest $true
foreach ($mbx in (Get-Mailbox -ResultSize unlimited)) { Get-InboxRule -Mailbox $mbx.DistinguishedName | where {($_.ForwardTo -ne $null) -or ($_.redirectto -ne $null) -or ($_.forwardasattachment -ne $null)} | select MailboxOwnerID,Name,ForwardTo | export-csv d:\ForwardRule.csv} -Notypeinformation
Send-MailMessage -To alias@domain.com -cc alias@domain.com -From anyid@domain.com -Subject “Forward To” -Attachments d:\ForwardRule.csv -SmtpServer specifytransportserver
*******************************************************
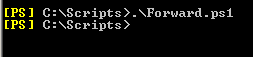
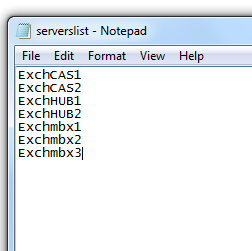
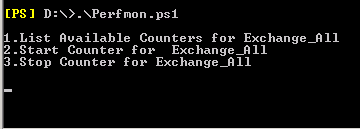
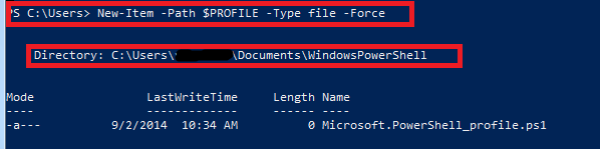
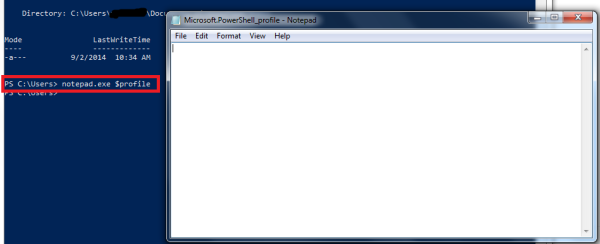
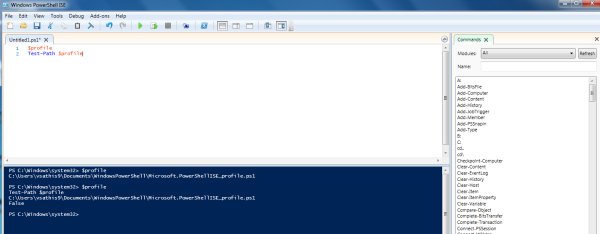
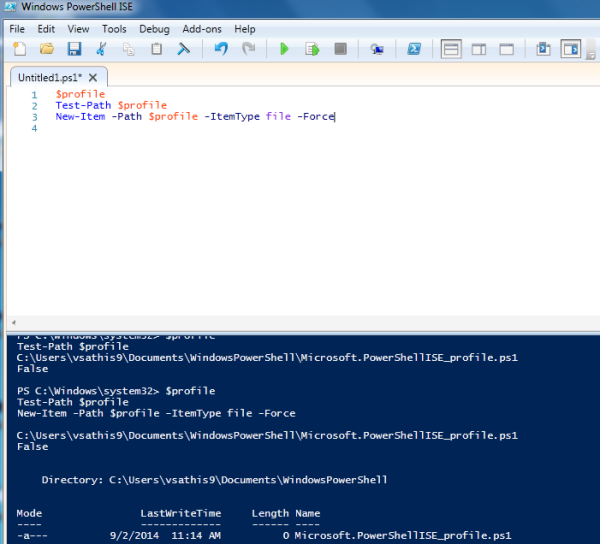
Copy the above text in a notepad and then save them as ps1. Navigate to the location where you saved it and then you can execute the command
Things you need to modify in the above script
Set the drive location for the csv file in a place where you wish to save.
For sending email in the to and cc field give user for whom you need this report to be sent
From address specify the address from where it needs to be sent and give the mailbox server as smtp server if it’s 2013 or hub server if it is 2010 or 2007.
Here is the example
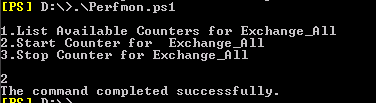
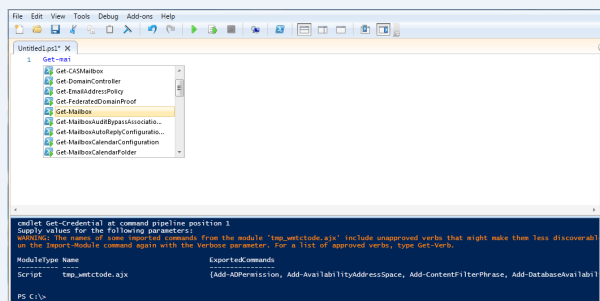
Just copy the code in text file and save it in ps1 format.
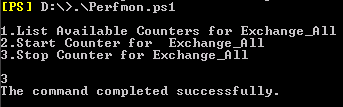
navigated to the location and ran.
Received the email
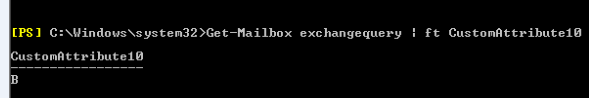
When we open the csv file the output is displayed for users who have forwardto,redirectto and forwardasattachment option set in outlook rules for external id’s.
Note:
This command pulls out rules from user’s mailbox only if they are enabled. If the user has a rule created and if he has disabled it temporarily then it won’t fetch that information.
Thanks
Sathish Veerapandian
MVP – Exchange Server