Like different DNS hosting suppliers, we have DNS facilitating choice both private and public in Microsoft Azure.We have Azure Provided DNS, Bring your own DNS and use Azure private DNS which is in review starting at now.
Azure Provided DNS: (Azure-provided name resolution)
With Azure provided DNS the deployment is a lot simpler, and no complex setup is required from our side.They come up with highly available model and they can be used with in conjunction with our DNS. There are few caveats in this model which is the DNS suffix can’t be changed since they are auto created and given from Azure. DNS Query Traffic is throttled for each VM’s which might need to be taken into consideration for intensive web applications. Thus Wins and Net Bios are likewise not Supported. At last, manual registration of DNS records isn’t supported.
To create Azure DNS – Login to Azure Portal – Search for DNS – Select DNS Zones- Click on create DNS Zone.
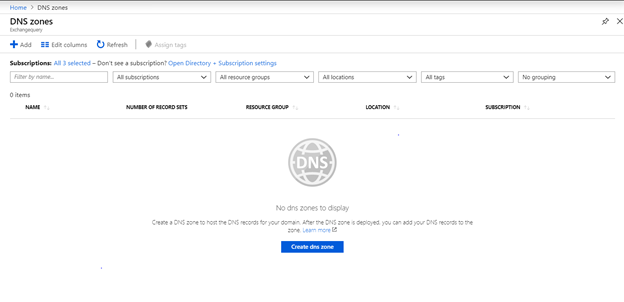
Key in the requested details and create

Once created we can see the name servers which are from Azure.So these Azure name servers are responsible to answer DNS queries for the hosted domain from the users on the internet.
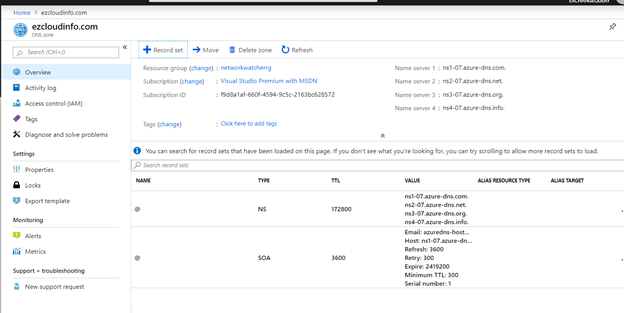
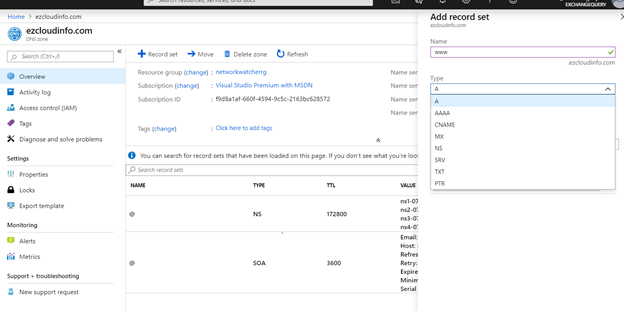
Now we have the option to add the record sets and once these records sets are created they will be available public.
To create DNS name from the Powershell we can use the below command
New-AzDNsZone -Name ezcloudinfo.com -ResourceGroupName Network-NG
To create a DNS Record Set we can use the below parameter
New-AzDnsRecordSet -Name www -RecordType A
Bring Your Own DNS:
Bring your own DNS is regularly utilized in hybrid connectivity scenarios which is connecting Azure assets to on-premise DNS system and connecting Azure to various DNS Networks. This is generally required in situations where our Azure cloud VM’s requires reverse lookup of on-premise internal IP’s or authentication is required in domain controller for applications running on VM in Azure.
The most crucial thing is that when we are implementing the bring your own DNS on Azure we need to turn of DNS Scavenging which will help us to prevent the accidental deletion of DNS records. Also, we need to enable DNS recursion and ensure port 53 is accessible from all the clients.
One crucial point to consider is that we must never specify our own DNS settings within the VM itself because the system is unaware of the settings for DNS. Instead there is configuration options within the virtual network settings which are at VNET level and will be applied to all resources in the network.
We need to register each VM in provided DNS service or configure the DNS servce to accept Dynamic DNS Queries.
We can configure the custom DNS as below from the Azure Portal.
Navigate to Azure Portal – Select the virtual networks that needs to use our own DNS – We will see the default Azure provided DNS.
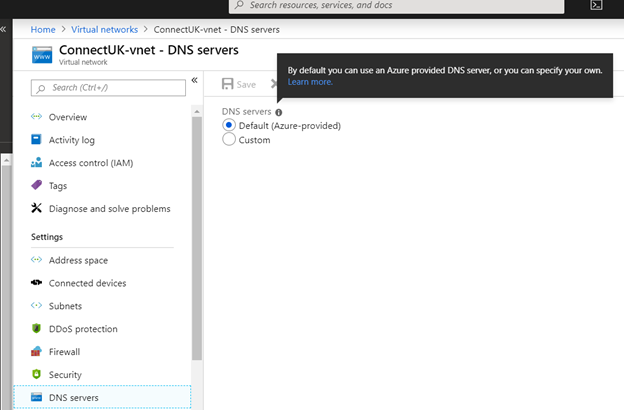
In-order to use our DNS select Custom and key in the DNS details on the required VNET.

The same steps is applicable for the individual VMs and in those cases we need to enter the DNS servers in the VM network interface.
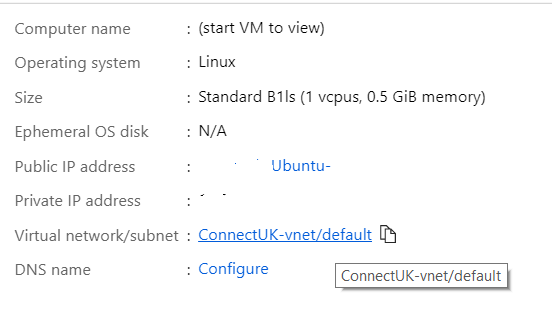
And change the DNS servers to our custom DNS.
The private DNS can be configured at the VNET , Network Interface level and not at the subnet level. So we need to configure these settings on each VM’s network interface.
Azure private DNS (Preview):
Presently Azure DNS likewise underpins Private DNS areas which is in review starting at now. This is a promising component to give DNS between private virtual networks.
With these private DNS Zones we can utilize our very own custom DNS names without the complexity nature of overseeing and keeping up our own DNS servers.
As of now the name resolution is supported up to ten virtual networks.If we need to resolve the VM names from multiple virtual networks the VMs in any other networks must be registered with the service manuallyAs of now the name resolution is supported up to ten virtual networks. As the name indicates these zones are not exposed to the internet and will be communicating only within the inter linked virtual networks.
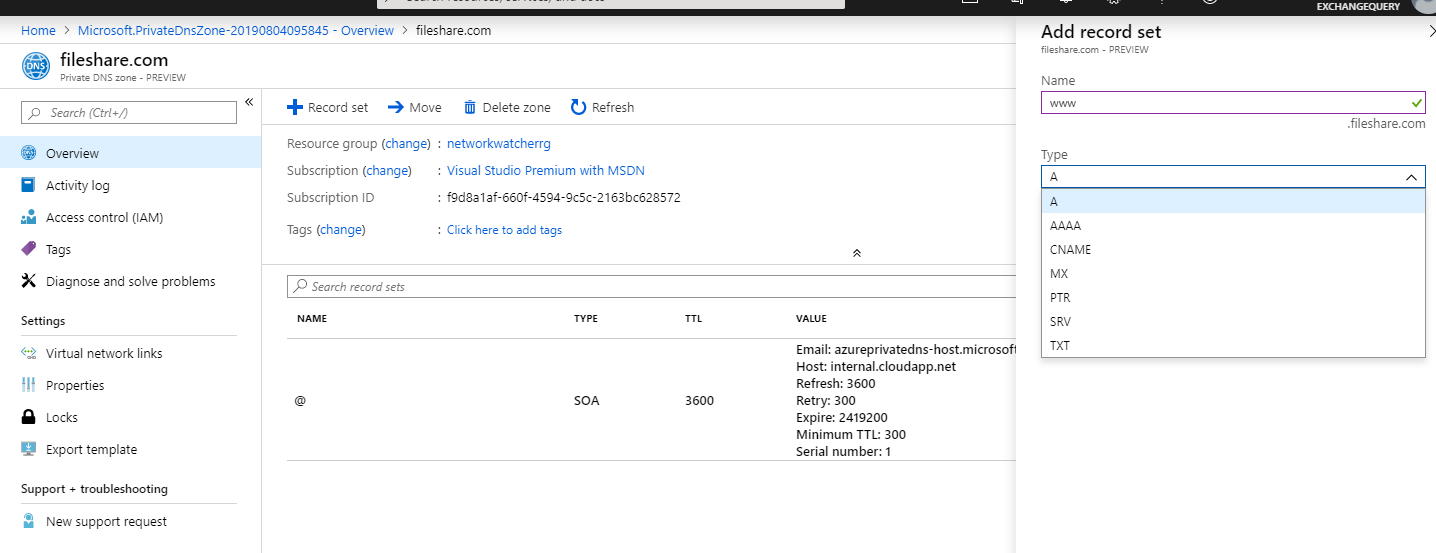
The procedure is similar like what we see on Azure DNS – Navigate to Azure portal – select private dns zones.

Once created we will see them to be a private DNS.
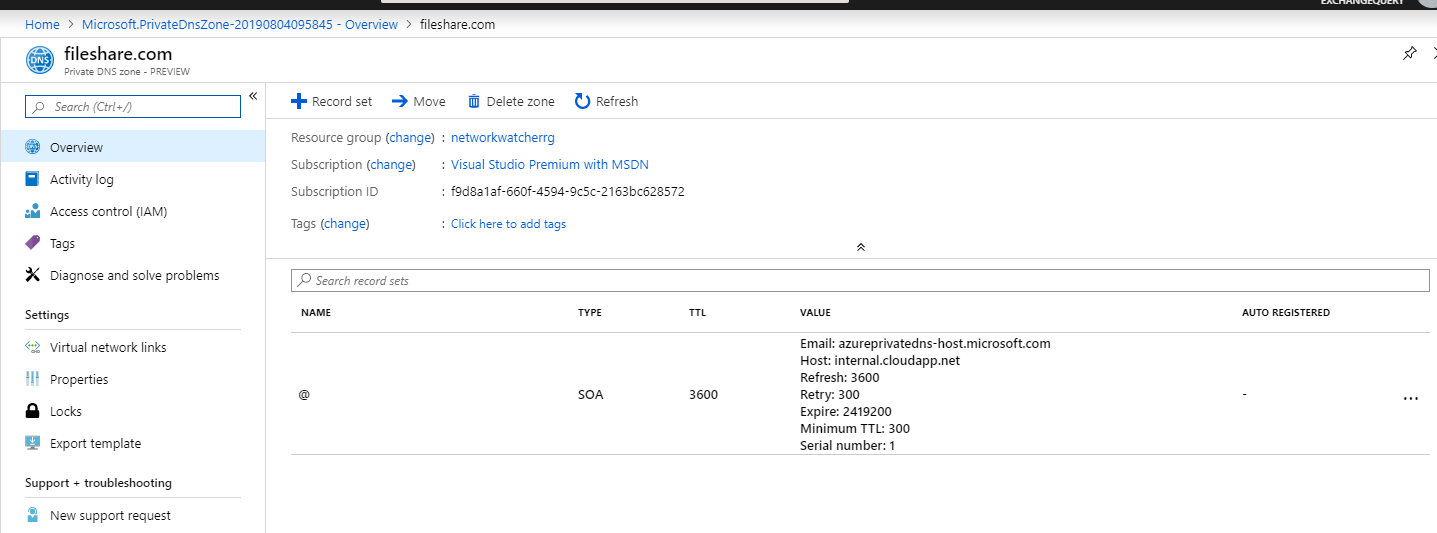
We have the options to create records sets which will be communicating between these interlinked Vnets.
Since this Azure private DNS is in review mode without Service Level Agreement it is prescribed not to move this out on production environments . Its better to play around and investigate the utilized cases which will help when it is rolled out live on production environments.
Additional Info:
IP address 168.63.129.16 is a virtual public IP address that is used to facilitate a communication channel to Azure platform. The public IP address 168.63.129.16 is used in all regions and all national clouds. This special public IP address is owned by Microsoft and will not change and offers below features.
1) Enables the VM Agent to communicate with the Azure platform.
2) Enables communication with the DNS virtual server to provide filtered name resolution.
3) Enables health probes from Azure load balancer.
4) Enables the VM to obtain a dynamic IP address from the DHCP service in Azure.
5) Azure DNS also supports importing and exporting zone files by using the az network zone import and export command lets. Importing zone files will create a new zone in the Azure DNS if they are new record sets or they are merged with existing if there is a zone already present with this name in the azure DNS.
Thanks & Regards
Sathish Veerapandian


Leave a comment