In this article we will be looking on how to Migrate from BES 4.0 to 5.0.
Below are the few technologies which have been improved much in BES 5.0.4 compared to earlier versions.
Advanced security features enhanced
BlackBerry Enterprise Server ensures sensitive information is transmitted in a highly protected environment.
Customizable user permissions increased
With over 500 IT policies and BlackBerry Balance technology, administrators can manage user settings, control groups and wirelessly adjust security levels and capabilities.
Stable Remote device management
Track and manage smart phones remotely, without interrupting business
Designed to meet the needs of enterprise and government, BlackBerry® Enterprise Server is for organizations that have an on premise email server and require a high level of IT control.
BlackBerry Enterprise Server can be run in environments alongside BlackBerry® Enterprise Server Express for organizations that only have a subset of users that require advanced IT management.
Includes BlackBerry® Balance™ technology to enable employees’ BlackBerry smart phones to be used for business and personal use without compromise.
Premigration Checklist
Infrastructure Network latency: Ensure there is no network latency in the environment.
Messaging Server/Service Location: Make sure the Messaging server is located in the same AD site.
Service accounts: Ensure the service accounts going to be used for BB account has full domain admin rights
LDAP (Kerberos) : Check for any LDAP errors by running DCDIAG
Microsoft SQL Server database mirroring: Plan accordingly whether we need db mirroring or it can run with the same setup or not according to the environment.
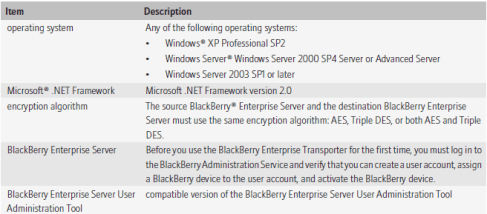
System Requirements
Supported Environments
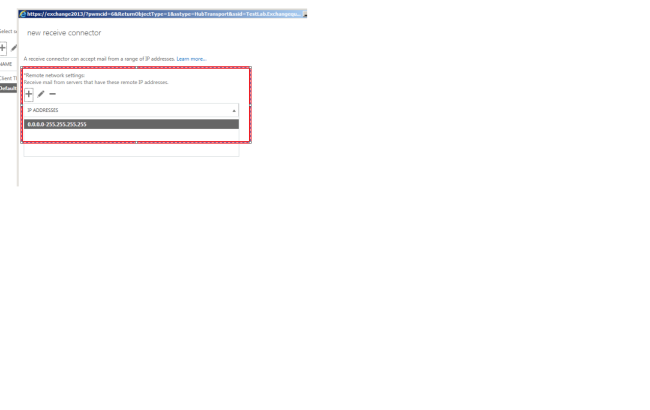
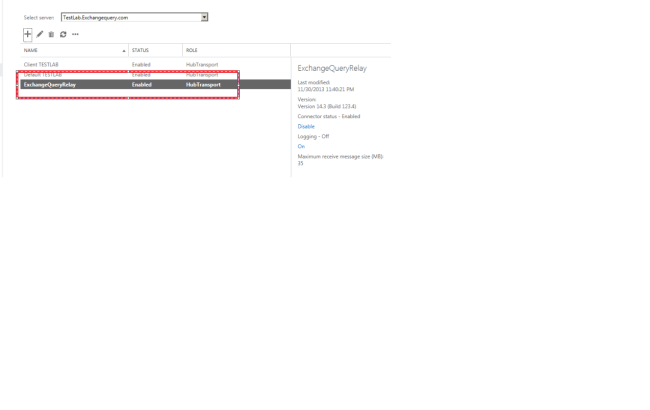
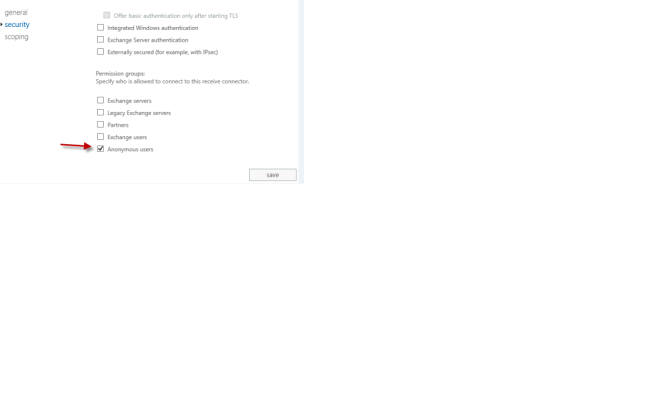
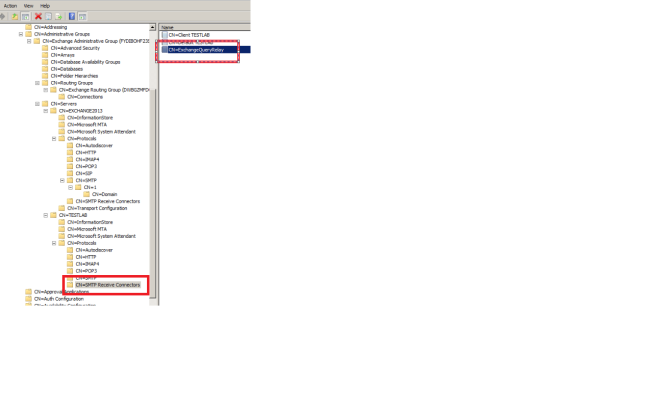
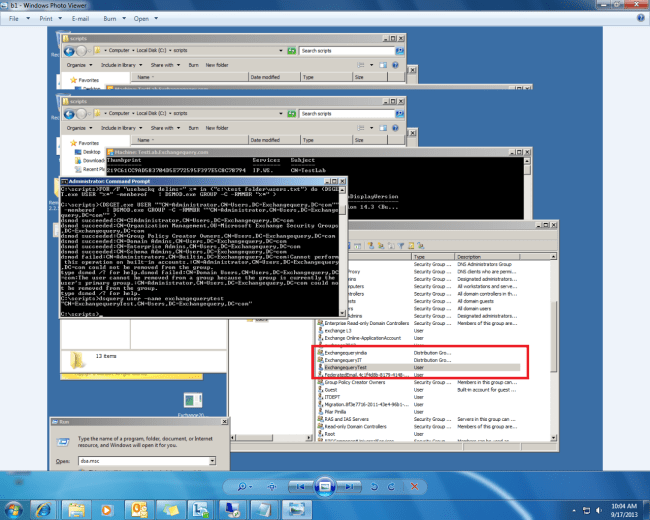
Preparing the source domain for migration process
Preparing the destination domain for migration process
Steps to use BET Tool for Migration.
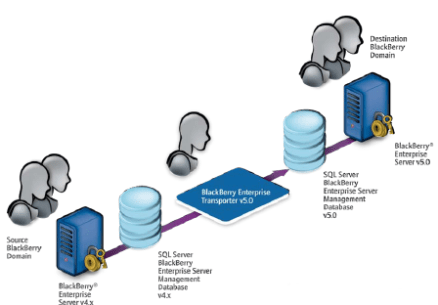
You can use the BlackBerry® Enterprise Transporter to move one or more user accounts from one BlackBerry Domain to a different Blackberry Domain
You can use the BlackBerry Enterprise Transporter when your organization upgrades the BlackBerry® Enterprise Server and you want to create a new BlackBerry Domain, or if you need to move user accounts between BlackBerry Domain instances. For example, if you want to upgrade your organization’s BlackBerry Enterprise Server from version 4.0 SP7 to version 5.0, you can create a separate Blackberry Domain version 5.0 and use the BlackBerry Enterprise Transporter to move your organization’s user accounts to the new Blackberry Configuration Database. You can also use the BlackBerry Enterprise Transporter to move user accounts from a production Blackberry Domain to a test BlackBerry Domain and back.
When you run the BlackBerry Enterprise Transporter, users do not need to delete BlackBerry device data or reactivate their Blackberry devices, if the BlackBerry Enterprise Transporter supports the BlackBerry® Device Software version that they are using. The destination BlackBerry Enterprise Server resends service books, and the BlackBerry devices can start receiving new messages after the BlackBerry devices receive the service books. Synchronization of organizer data and calendar information over the wireless network might occur after the migration process completes.
BET works in 2 modes
Live
BES instances in both BB Domain instances must use different SRP IDs.
Move user accounts when the BES instances in both the destination BB Domain and the source BB Domain are running.
Bulk
During the migration process BB Enterprise Server instances in both the source and the destination domains must be turned off.
In the destination BB Domain, BB Administration Service must be running.
During the migration process, based on the source BB server, the BB Enterprise Transporter searches the source BB Configuration Database for all user accounts that are associated with the BB Enterprise Server, and moves them.
Configure the destination BB Enterprise Server instances to use the same
SRP IDs that the source BB Enterprise Server instances use.
Advantages of BET tool During Migration
Users do not need to delete BB device data or reactivate their BB.
The destination BB Enterprise Server resends service books, and the BB devices can start receiving new messages after the BB devices receive the service books.
Synchronization of organizer data and calendar information over the wireless network might occur after the migration process completes.
Preview user move to check for potential errors
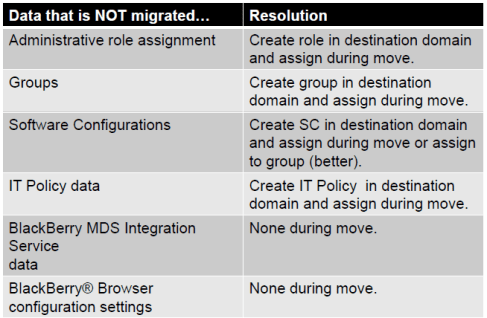
Below steps need to be done for the data that is not migrated
BB Enterprise Transporter (BET) performs two validations
Global Validation
BAS is installed in destination BB Domain.
Sends a test BB Administration Service command to verify that the BB Administration Service is available and can respond.
User Validation
User account is associated with a valid email address.
Account does exist in the source BB Domain and does not exist in the destination BB Domain.
IT Policy can be applied to the BB Smartphone.
BB device is running an unspecified version of the BB Device Software
BB device is operating on BB Device Software version 4.0.2, and less the ITPolicyKeyMapping table does not exist.
BB device is operating on BB Device Software version 4.3.0
Preparing the move user accounts with the BB Enterprise Transporter:
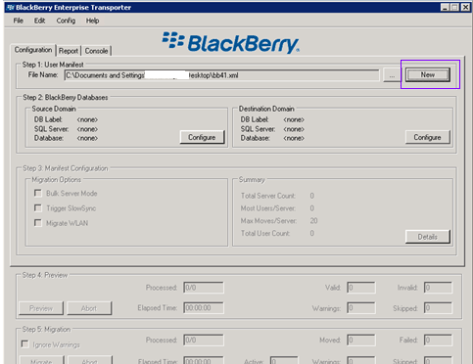
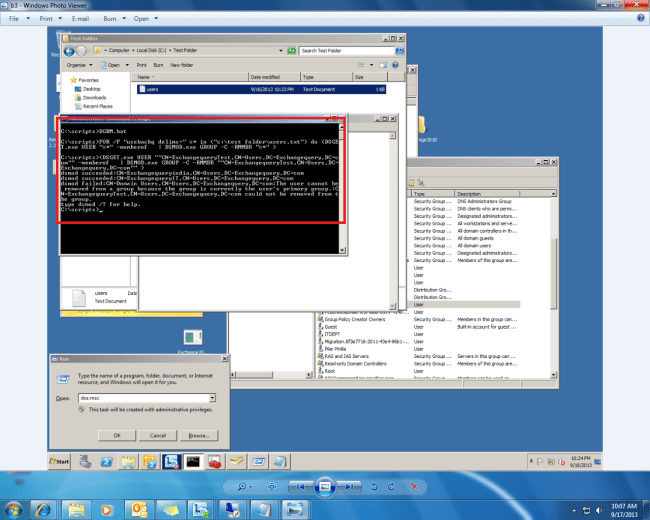
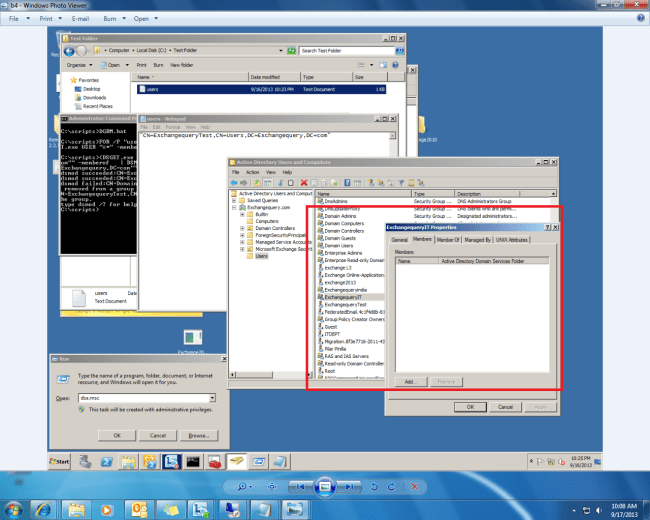
Create the manifest file.
1. Configure the source and destination BB Configuration Database instances.
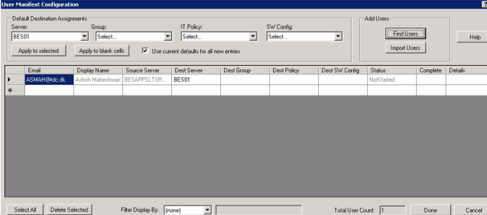
2. Configure the default settings for user accounts in the destination BB Domain.
3. Selecting the user accounts to move to the destination BB Domain or select all user accounts associated with a source BB Enterprise Server.
4. Move the user accounts
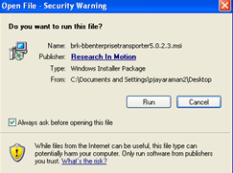
Installing the BB Enterprise Transporter
1. Create a folder to store the BB Enterprise Transporter files.
2. In a browser, visit na.BB.com/eng/support/server_resourcekit.jsp.
3. Download the BB Enterprise Transporter installation package.
4. Extract the contents of the installation package to the folder that you created.
5. Double-click the brk-bbenterprisetransporter.msi file.
6. Complete the instructions on the screen
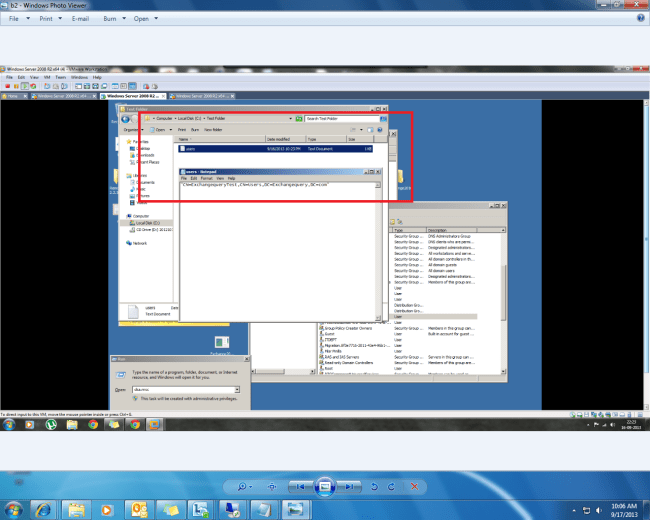
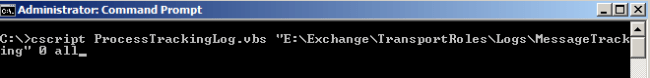
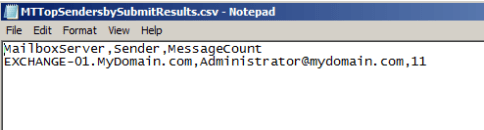
Create a Manifest file in xml
Configure the source database
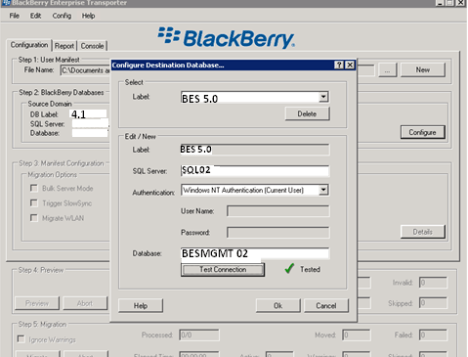
Configure Destination database
Verify the server names and database click on details to choose users for migration
Click on find users choose users and done
Verify the user list and click on done
Click on Preview to validate the user
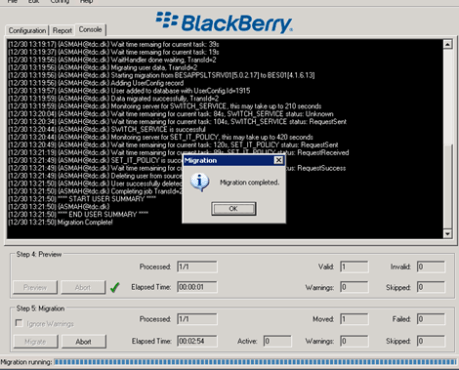
Migration Progress and completion
Checklist to be performed before Migration
Backup current environment.
Confirm pre-requisites.
Start BB Enterprise Server setup application on a new server.
Create new BB Configuration Database.
Restart server & Complete configuration.
Recreate IT Policy and Software Configurations in BES 5.0 environment.
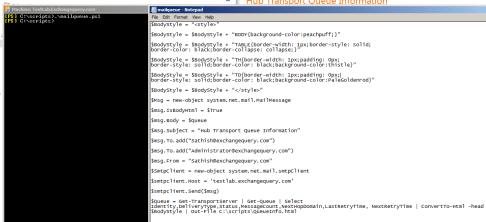
Shutdown services on BB Enterprise Server 4.x.
Start the BAS service on BB Enterprise Server 5.0. Move users with BET (bulk mode)
Conclusion
BES 5.0 infrastructure can be deployed independent of already existing BES 4.X deployment.
•Separate BB configuration database created for BES 5.0 environment.
•IT Policy(s), Application Control Policy(s), and Software Configurations are created and validated in BES 5.0 environment.
•BB User(s) is migrated using the BB Enterprise Transport (BET) Tool Live mode or Bulk mode.
• We can view, but not change, the properties of previous versions of the BB MDS Integration Service, BB MDS Connection Service, and BB Collaboration Service from BAS.
- Before you try to move the user accounts, upgrade the source BB Enterprise Server for Microsoft Exchange to version 4.1 SP6 MR5 or later.