Teams encrypts all communication by default with industry-standard technologies including Transport Layer Security (TLS) and Secure Real-Time Transport Protocol (SRTP). By default TLS authenticates all traffic and encrypts them. SRTP is used for media traffic and also encrypted. And by default they are definitely Trustworthy and this end to end encryption is definitely not required unless there is a specific business case.
Last month Microsoft announced the public preview of the end to end encryption as per this blog
The goal of end-to-end encryption is to prevent data from being read or secretly manipulated by anybody other than the sender and recipient. The sender encrypts the calls, chats & files, but the third party or even the service provider has no way of decrypting them and stores them encrypted. The recipients obtain and decrypt the encrypted data on their own.
There may be a situation when a few participants are dealing with business-critical data or sensitive information, and they want more increased security to meet their compliance and regulatory obligations. In some circumstances, end-to-end encryption can be used to accommodate those scenarios, and it can be enabled exclusively for those users who are specifically targeted.
Enabling end to end encryption can be done in few steps from the Teams Powershell module.
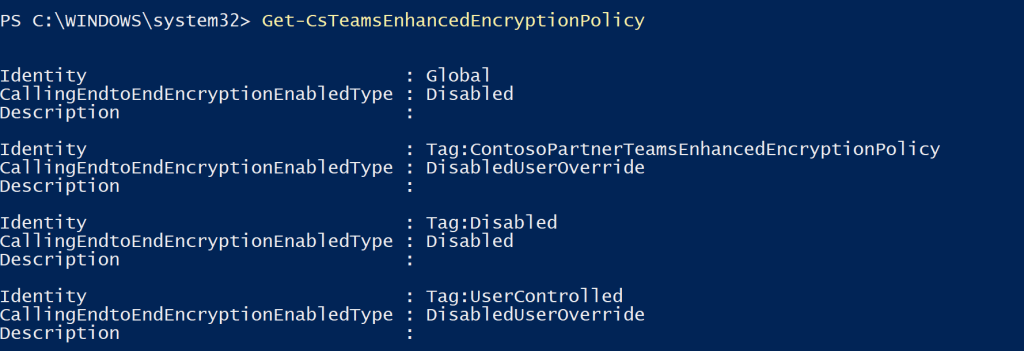
These are below encryption policies which are not assigned by default to any users. Ignore the second one Tag:ContosoPartnerTeamsEnhancedEncryptionPolicy as it was created for testing the new policy creation.
Get-CsTeamsEnhancedEncryptionPolicy can be used to check the default policies.
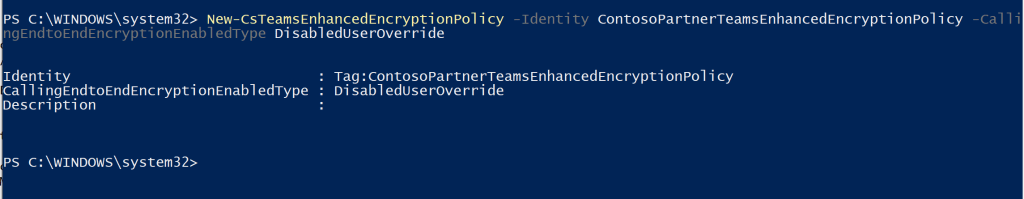
Creating the new policy can be done with the below command
New-CsTeamsEnhancedEncryptionPolicy -Identity ContosoPartnerTeamsEnhancedEncryptionPolicy -CallingEndtoEndEncryptionEnabledType DisabledUserOverride
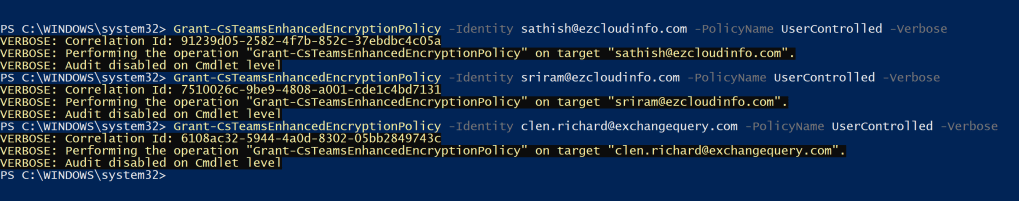
We have to assign the policy for the users to be working. One important point to consider is that this policy needs to be enabled for users who will be requiring the end to end encryption. In our example we have chosen 3 users for testing.
Grant-CsTeamsEnhancedEncryptionPolicy -Identity sathish@ezcloudinfo.com -PolicyName UserControlled
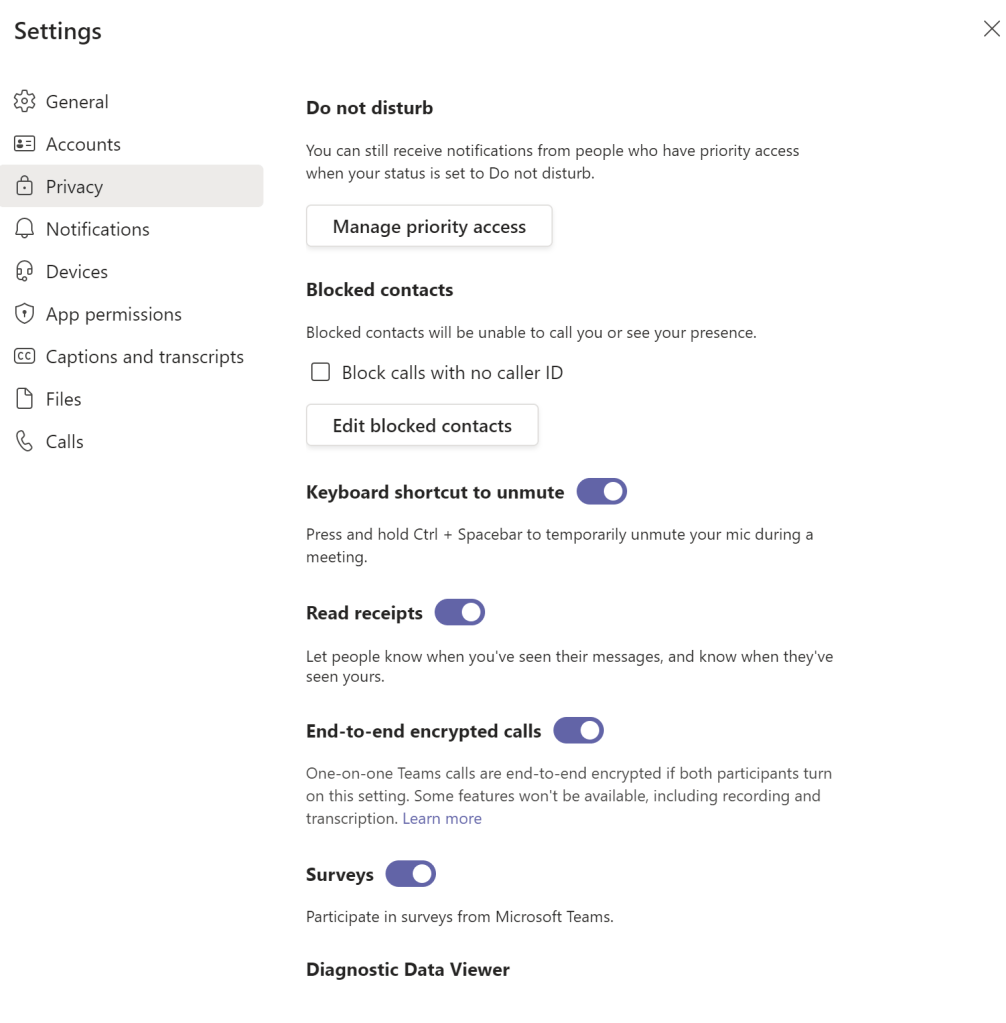
Once after its enabled the policy is not turned on by default to the end users. End users needs to enable them from the Teams Client by navigating to settings – privacy – And after assigning the policy to the user End to End encrypted calls options will be showing and we need to turn them on.
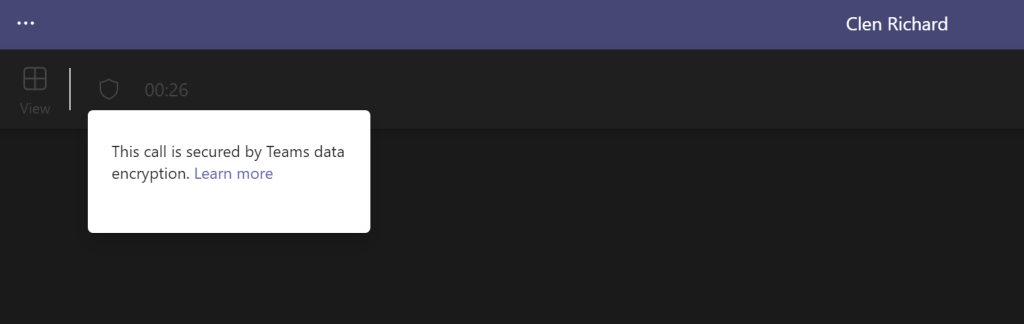
Finally after enabling this policy on both sender and receiver clients after making a test call we can see the information that states the call is being encrypted. In a ongoing call we see the security pad lock and when clicking on them we get the below message which informs us that the call is secured by Teams data encryption.
At the moment of writing this blog the E2E calls are limited only to direct peer to peer calls. Audio,Video and screen sharing during this session is encrypted and chat sessions will be secured by Microsoft 365. E2E encryption is not applicable for PSTN calls.
And advanced call features – Recording,Captions & Transcription, Call Transfer, Call merge, call park , consult then transfer, Call companion and adding a partipants are not available at this moment.
And if we have enabled the compliance recording for few users then we cannot enable the E2E encryption for those users.
Regards
Sathish Veerapandian


Leave a comment